Premium Only Content
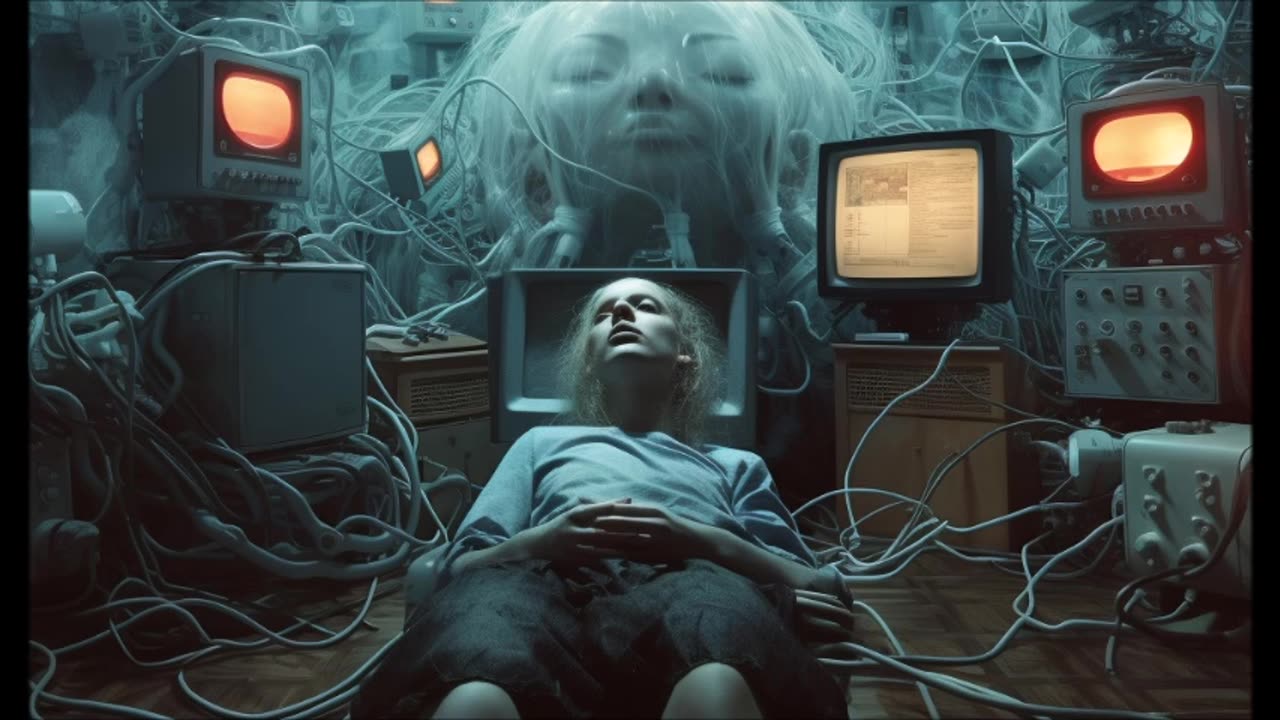
Electronic Nightmare: The Dark Side of the Computer Age (1981)
Read the book: https://amzn.to/46RFrv9
"Electronic Nightmare" by John Wicklein, published in 1981, delves into the potential dangers and risks associated with the rapid advancement of electronic technology. Wicklein examines how our increasing reliance on technology might lead to unforeseen consequences, exploring the potential for societal disruptions, privacy infringements, and ethical dilemmas.
The book takes a critical look at the implications of widespread computerization, addressing concerns about data security, surveillance, and the potential loss of individual autonomy in a technologically driven world.
Global mass surveillance can be defined as the mass surveillance of entire populations across national borders.[1]
Its existence was not widely acknowledged by governments and the mainstream media until the global surveillance disclosures by Edward Snowden triggered a debate about the right to privacy in the Digital Age.[2][3]
Its roots can be traced back to the middle of the 20th century when the UKUSA Agreement was jointly enacted by the United Kingdom and the United States, which later expanded to Canada, Australia, and New Zealand to create the present Five Eyes alliance.[4] The alliance developed cooperation arrangements with several "third-party" nations. Eventually, this resulted in the establishment of a global surveillance network, code-named "ECHELON" (1971).[5][6]
Historical background
Main article: Origins of global surveillance
The origins of global surveillance can be traced back to the late 1940s after the UKUSA Agreement was collaboratively enacted by the United Kingdom and the United States, which eventually culminated in the creation of the global surveillance network code-named "ECHELON" in 1971.[5][6]
In the aftermath of the 1970s Watergate affair and a subsequent congressional inquiry led by Sen. Frank Church,[7] it was revealed that the NSA, in collaboration with Britain's GCHQ, had routinely intercepted the international communications of prominent anti-Vietnam War leaders such as Jane Fonda and Dr. Benjamin Spock.[8] Decades later, a multi-year investigation by the European Parliament highlighted the NSA's role in economic espionage in a report entitled 'Development of Surveillance Technology and Risk of Abuse of Economic Information', in 1999.[9]
However, for the general public, it was a series of detailed disclosures of internal NSA documents in June 2013 that first revealed the massive extent of the NSA's spying, both foreign and domestic. Most of these were leaked by an ex-contractor, Edward Snowden. Even so, a number of these older global surveillance programs such as PRISM, XKeyscore, and Tempora were referenced in the 2013 release of thousands of documents.[10] Many countries around the world, including Western Allies and member states of NATO, have been targeted by the "Five Eyes" strategic alliance of Australia, Canada, New Zealand, the UK, and the United States—five English-speaking Western countries aiming to achieve Total Information Awareness by mastering the Internet with analytical tools such as the Boundless Informant.[11] As confirmed by the NSA's director Keith B. Alexander on 26 September 2013, the NSA collects and stores all phone records of all American citizens.[12] Much of the data is kept in large storage facilities such as the Utah Data Center, a US $1.5 billion megaproject referred to by The Wall Street Journal as a "symbol of the spy agency's surveillance prowess."[13]
Today, this global surveillance system continues to grow. It now collects so much digital detritus – e-mails, calls, text messages, cellphone location data and a catalog of computer viruses - that the N.S.A. is building a 1-million-square-foot facility in the Utah desert to store and process it.
— The New York Times[14] (August 2012)
On 6 June 2013, Britain's The Guardian newspaper began publishing a series of revelations by an as yet unknown American whistleblower, revealed several days later to be ex-CIA and ex-NSA-contracted systems analyst Edward Snowden. Snowden gave a cache of documents to two journalists, Glenn Greenwald and Laura Poitras. Greenwald later estimated that the cache contains 15,000–20,000 documents, some very large and detailed, and some very small.[15][16] In over two subsequent months of publications, it became clear that the NSA had operated a complex web of spying programs that allowed it to intercept Internet and telephone conversations from over a billion users from dozens of countries around the world. Specific revelations were made about China, the European Union, Latin America, Iran and Pakistan, and Australia and New Zealand, however, the published documentation reveals that many of the programs indiscriminately collected bulk information directly from central servers and Internet backbones, which almost invariably carry and reroute information from distant countries.[citation needed]
Due to this central server and backbone monitoring, many of the programs overlapped and interrelated with one another. These programs were often carried out with the assistance of US entities such as the United States Department of Justice and the FBI,[17] were sanctioned by US laws such as the FISA Amendments Act, and the necessary court orders for them were signed by the secret Foreign Intelligence Surveillance Court. Some of the NSA's programs were directly aided by national and foreign intelligence agencies, Britain's GCHQ and Australia's ASD, as well as by large private telecommunications and Internet corporations, such as Verizon, Telstra,[18] Google, and Facebook.[19]
Snowden's disclosures of the NSA's surveillance activities are a continuation of news leaks which have been ongoing since the early 2000s. One year after the September 11, 2001, attacks, former U.S. intelligence official William Binney was publicly critical of the NSA for spying on U.S. citizens.[20]
Further disclosures followed. On 16 December 2005, The New York Times published a report under the headline "Bush Lets U.S. Spy on Callers Without Courts."[21] In 2006, further evidence of the NSA's domestic surveillance of U.S. citizens was provided by USA Today. The newspaper released a report on 11 May 2006, regarding the NSA's "massive database" of phone records collected from "tens of millions" of U.S. citizens. According to USA Today, these phone records were provided by several telecom companies such as AT&T, Verizon, and BellSouth.[22] In 2008, the security analyst Babak Pasdar revealed the existence of the so-called "Quantico circuit" that he and his team discovered in 2003 when brought on to update the carrier's security system. The circuit provided the U.S. federal government with a backdoor into the network of an unnamed wireless provider, which was later independently identified as Verizon.[23]
Snowden's disclosures
Further information: Global surveillance disclosures (2013–present)
Snowden made his first contact with journalist Glenn Greenwald of The Guardian in late 2012.[24] The timeline of mass surveillance disclosures by Snowden continued throughout the entire year of 2013.
By category
Main article: Global surveillance by category
Documents leaked by Snowden in 2013 include court orders, memos, and policy documents related to a wide range of surveillance activities.
Purposes
According to the April 2013 summary of documents leaked by Snowden, other than to combat terrorism, these surveillance programs were employed to assess the foreign policy and economic stability of other countries,[25] and to gather "commercial secrets".[26]
In a statement addressed to the National Congress of Brazil in early August 2013, journalist Glenn Greenwald maintained that the U.S. government had used counter-terrorism as a pretext for clandestine surveillance in order to compete with other countries in the "business, industrial and economic fields".[27][28] In a December 2013 letter to the Brazilian government, Snowden wrote that "These programs were never about terrorism: they're about economic spying, social control, and diplomatic manipulation. They're about power."[29] According to a White House panel member, the NSA didn't stop any terrorist attack.[30] However the NSA chief stated that surveillance programs stopped 54 terrorist plots.[31]
In an interview with Der Spiegel published on 12 August 2013, former NSA Director Michael Hayden admitted that "We (the NSA) steal secrets. We're number one in it". Hayden also added: "We steal stuff to make you safe, not to make you rich".[25]
According to documents seen by the news agency Reuters, these "secrets" were subsequently funneled to authorities across the nation to help them launch criminal investigations of Americans.[32] Federal agents are then instructed to "recreate" the investigative trail in order to "cover up" where the information originated.[32]
According to the congressional testimony of Keith B. Alexander, Director of the National Security Agency, one of the purposes of its data collection is to store all the phone records inside a place that can be searched and assessed at all times. When asked by Senator Mark Udall if the goal of the NSA is to collect the phone records of all Americans, Alexander replied, "Yes, I believe it is in the nation's best interest to put all the phone records into a lockbox that we could search when the nation needs to do it."[33]
Targets and methods
Collection of metadata and other content
In the United States, the NSA is collecting the phone records of more than 300 million Americans.[34] The international surveillance tool XKeyscore allows government analysts to search through vast databases containing emails, online chats and the browsing histories of millions of individuals.[35][36][37] Britain's global surveillance program Tempora intercepts the fibre-optic cables that form the backbone of the Internet.[38] Under the NSA's PRISM surveillance program, data that has already reached its final destination would be directly harvested from the servers of the following U.S. service providers: Microsoft, Yahoo!, Google, Facebook, Paltalk, AOL, Skype, YouTube, and Apple Inc.[39]
Contact chaining
The New York Times, citing documents leaked by Snowden, reported in September 2013 on the NSA's "push to exploit phone and e-mail data of Americans after it lifted restrictions in 2010", which enables "large-scale graph analysis on very large sets of communications metadata".[40] This slide from an NSA presentation shows one of the methods in which the agency uses e-mail and phone data to analyze the relationship network of a target. According to The Times, the NSA can "augment the communications data with material from public, commercial and other sources, including bank codes, insurance information, Facebook profiles, passenger manifests, voter registration rolls and GPS location information, as well as property records and unspecified tax data".[41] Such types of data were collected from U.S. citizens as well as foreign nationals.[41]
Contact chaining is a method that involves utilizing data related to social links among individuals, including call logs that connect phone numbers with each other, in order to pinpoint individuals associated with criminal groups. However, a lack of privacy guidelines can result in this process amassing an extensive portion of user data.[42]
The NSA uses the analysis of phone call and e-mail logs of American citizens to create sophisticated graphs of their social connections that can identify their associates, their locations at certain times, their traveling companions and other personal information.[41]
According to top secret NSA documents leaked by Snowden, during a single day in 2012, the NSA collected e-mail address books from:
22,881 Gmail accounts[43]
82,857 Facebook accounts[43]
105,068 Hotmail accounts[43]
444,743 Yahoo! accounts[43]
Each day, the NSA collects contacts from an estimated 500,000 buddy lists on live-chat services as well as from the inbox displays of Web-based e-mail accounts.[43] Taken together, the data enables the NSA to draw detailed maps of a person's life based on their personal, professional, religious and political connections.[43]
Data transfer
Federal agencies in the United States: Data gathered by these surveillance programs is routinely shared with the U.S. Federal Bureau of Investigation (FBI) and the U.S. Central Intelligence Agency (CIA).[44] In addition, the NSA supplies domestic intercepts to the Drug Enforcement Administration (DEA), Internal Revenue Service (IRS), and other law enforcement agencies.[32]
Foreign countries: As a result of the NSA's secret treaties with foreign countries, data gathered by its surveillance programs are routinely shared with countries who are signatories to the UKUSA Agreement. These foreign countries also help to operate several NSA programs such as XKEYSCORE. (See International cooperation.)
Financial payments monitoring
A special branch of the NSA called "Follow the Money" (FTM) monitors international payments, banking and credit card transactions and later stores the collected data in the NSA's financial databank, "Tracfin".[45]
Mobile phone location tracking
Mobile phone tracking refers to the act of attaining the position and coordinates of a mobile phone. According to The Washington Post, the NSA has been tracking the locations of mobile phones from all over the world by tapping into the cables that connect mobile networks globally and that serve U.S. cellphones as well as foreign ones. In the process of doing so, the NSA collects more than 5 billion records of phone locations on a daily basis. This enables NSA analysts to map cellphone owners' relationships by correlating their patterns of movement over time with thousands or millions of other phone users who cross their paths.[46][47][48][49][50][51][52]
In order to decode private conversations, the NSA has cracked the most commonly used cellphone encryption technology, A5/1. According to a classified document leaked by Snowden, the agency can "process encrypted A5/1" even when it has not acquired an encryption key.[53] In addition, the NSA uses various types of cellphone infrastructure, such as the links between carrier networks, to determine the location of a cellphone user tracked by Visitor Location Registers.[54]
Infiltration of smartphones
As worldwide sales of smartphones grew rapidly, the NSA decided to take advantage of the smartphone boom. This is particularly advantageous because the smartphone contains a variety of data sets that would interest an intelligence agency, such as social contacts, user behaviour, interests, location, photos and credit card numbers and passwords.[55]
According to the documents leaked by Snowden, the NSA has set up task forces assigned to several smartphone manufacturers and operating systems, including Apple Inc.'s iPhone and iOS operating system, as well as Google's Android mobile operating system.[55] Similarly, Britain's GCHQ assigned a team to study and crack the BlackBerry.[55] In addition, there are smaller NSA programs, known as "scripts", that can perform surveillance on 38 different features of the iOS 3 and iOS 4 operating systems. These include the mapping feature, voicemail and photos, as well as Google Earth, Facebook and Yahoo! Messenger.[55]
Infiltration of commercial data centers
In contrast to the PRISM surveillance program, which is a front-door method of access that is nominally approved by the FISA court, the MUSCULAR surveillance program is noted to be "unusually aggressive" in its usage of unorthodox hacking methods to infiltrate Yahoo! and Google data centres around the world. As the program is operated overseas (United Kingdom), the NSA presumes that anyone using a foreign data link is a foreigner, and is, therefore, able to collect content and metadata on a previously unknown scale from U.S. citizens and residents.[56] According to the documents leaked by Snowden, the MUSCULAR surveillance program is jointly operated by the NSA and Britain's GCHQ agency.[57] (See International cooperation.)
Infiltration of anonymous networks
The Five Eyes have made repeated attempts to spy on Internet users communicating in secret via the anonymity network Tor. Several of their clandestine operations involve the implantation of malicious code into the computers of anonymous Tor users who visit infected websites. In some cases, the NSA and GCHQ have succeeded in blocking access to the anonymous network, diverting Tor users to insecure channels. In other cases, the NSA and the GCHQ were able to uncover the identity of these anonymous users.[58][59][60][61][62][63][64][65][66]
Monitoring of hotel reservation systems
Under the Royal Concierge surveillance program, Britain's GCHQ agency uses an automated monitoring system to infiltrate the reservation systems of at least 350 luxury hotels in many different parts of the world.[67] Other related surveillance programs involve the wiretapping of room telephones and fax machines used in targeted hotels, as well as the monitoring of computers, hooked up to the hotel network.[67]
Virtual reality surveillance
The U.S. National Security Agency (NSA), the U.S. Central Intelligence Agency (CIA), and Britain's Government Communications Headquarters (GCHQ) have been conducting surveillance on the networks of many online games, including massively multiplayer online role-playing games (MMORPGs) such as World of Warcraft, as well as virtual worlds such as Second Life, and the Xbox gaming console.[68]
Political Espionage
According to the April 2013 summary of disclosures, the NSA defined its "intelligence priorities" on a scale of "1" (highest interest) to "5" (lowest interest).[25] It classified about 30 countries as "3rd parties", with whom it cooperates but also spies on:
Main targets: China, Russia, Iran, Pakistan and Afghanistan were ranked highly on the NSA's list of spying priorities, followed by France, Germany, Japan, and Brazil. The European Union's "international trade" and "economic stability" are also of interest.[25] Other high priority targets include Cuba, Israel, and North Korea.[69]
Irrelevant: From a US intelligence perspective, countries such as Cambodia, Laos and Nepal were largely irrelevant, as were governments of smaller European Union countries such as Finland, Denmark, Croatia and the Czech Republic.[25]
Other prominent targets included members and adherents of the Internet group known as "Anonymous",[25] as well as potential whistleblowers.[70] According to Snowden, the NSA targeted reporters who wrote critically about the government after 9/11.[71]
As part of a joint operation with the Central Intelligence Agency (CIA), the NSA deployed secret eavesdropping posts in eighty U.S. embassies and consulates worldwide.[72] The headquarters of NATO were also used by NSA experts to spy on the European Union.[73]
In 2013, documents provided by Edward Snowden revealed that the following intergovernmental organizations, diplomatic missions, and government ministries have been subjected to surveillance by the "Five Eyes":
Country/
Organization Target Method(s)
Brazil Ministry of Energy Collection of metadata records by the Communications Security Establishment of Canada (CSEC)[74]
France Ministry of Foreign and European Affairs Infiltration of virtual private networks (VPN)[75]
Embassy of France in Washington, D.C.
Germany Embassy of Germany in Rwanda[76]
Italy Embassy of Italy in Washington, D.C.
Installation of physical implants[77]
Copying of entire hard disk drives[77]
India Embassy of India in Washington, D.C.
Copying entire hard disk drives[78]
Picking data from screenshots[78]
Permanent Representative of India to the United Nations
Mexico Secretariat of Public Security
Hacking of e-mail accounts as part of an operation code-named "Whitetamale"[79]
European Union Council of the European Union in Brussels
Installation of covert listening devices[80]
Hacking and infiltration of virtual private networks[81]
Disk cloning[81]
Delegation to the United Nations in New York
Delegation to the United States in Washington, D.C.
United Nations United Nations Headquarters
Hacking of encrypted communications[81]
Infiltration of internal video conferences[81]
International Atomic Energy Agency (IAEA)
United Nations Development Programme (UNDP)[76]
United Nations Children's Fund (UNICEF)[76]
International Cooperation
The "Five Eyes" of Australia, Canada, New Zealand, the United Kingdom and the United States
During World War II, the BRUSA Agreement was signed by the governments of the United States and the United Kingdom for the purpose of intelligence sharing.[82] This was later formalized in the UKUSA Agreement of 1946 as a secret treaty. The full text of the agreement was released to the public on 25 June 2010.[83]
Although the treaty was later revised to include other countries such as Denmark, Germany, Ireland, Norway, Turkey, and the Philippines,[83] most of the information sharing has been performed by the so-called "Five Eyes",[84] a term referring to the following English-speaking western democracies and their respective intelligence agencies:
Australia – The Australian Signals Directorate of Australia[84]
Canada – The Communications Security Establishment of Canada[84]
New Zealand – The Government Communications Security Bureau of New Zealand[84]
United Kingdom – The Government Communications Headquarters of the United Kingdom, which is widely considered to be a leader in traditional spying due to its influence on countries that were once part of the British Empire.[84]
United States – The National Security Agency of the United States, which has the biggest budget and the most advanced technical abilities among the "five eyes".[84]
Top secret documents leaked by Snowden revealed that the "Five Eyes" have gained access to the majority of Internet and telephone communications flowing throughout Europe, the United States, and other parts of the world.
Left: SEA-ME-WE 3, which runs across the Afro-Eurasian supercontinent from Japan to Northern Germany, is one of the most important submarine cables accessed by the "Five Eyes". Singapore, a former British colony in the Asia-Pacific region (blue dot), plays a vital role in intercepting Internet and telecommunications traffic heading from Australia/Japan to Europe, and vice versa. An intelligence-sharing agreement between Singapore and Australia allows the rest of the "Five Eyes" to gain access to SEA-ME-WE 3.[85]
Right: TAT-14, a telecommunications cable linking Europe with the United States, was identified as one of few assets of "Critical Infrastructure and Key Resources" of the US on foreign territory. In 2013, it was revealed that British officials "pressured a handful of telecommunications and Internet companies" to allow the British government to gain access to TAT-14.[86]
NSA lists "Approved SIGINT countries" which are divided into two groups by their cooperation level with the NSA.
Second Parties
Third Parties
According to the leaked documents, aside from the Five Eyes, most other Western countries have also participated in the NSA surveillance system and are sharing information with each other.[87] In the documents the NSA lists "approved SIGINT partners" which are partner countries in addition to the Five Eyes. Glenn Greenwald said that the "NSA often maintains these partnerships by paying its partner to develop certain technologies and engage in surveillance, and can thus direct how the spying is carried out." These partner countries are divided into two groups, "Second Parties" and "Third Parties". The Second Parties are doing comprehensive cooperation with the NSA, and the Third Parties are doing focused cooperation.[88][89] However, being a partner of the NSA does not automatically exempt a country from being targeted by the NSA itself. According to an internal NSA document leaked by Snowden, "We (the NSA) can, and often do, target the signals of most 3rd party foreign partners."[90]
Australia
Pine Gap, near the Australian town of Alice Springs, is run by the CIA and it is part of the global surveillance program ECHELON.[91][92]
The Australian Signals Directorate (ASD), formerly known as the Defence Signals Directorate (DSD), shares information on Australian citizens with the other members of the UKUSA Agreement. According to a 2008 Five Eyes document leaked by Snowden, data of Australian citizens shared with foreign countries include "bulk, unselected, unminimised metadata" as well as "medical, legal or religious information".[93]
In close cooperation with other members of the Five Eyes community, the ASD runs secret surveillance facilities in many parts of Southeast Asia without the knowledge of Australian diplomats.[94] In addition, the ASD cooperates with the Security and Intelligence Division (SID) of the Republic of Singapore in an international operation to intercept underwater telecommunications cables across the Eastern Hemisphere and the Pacific Ocean.[95]
In March 2017 it was reported that, on advice from the Five Eyes intelligence alliance, more than 500 Iraqi and Syrian refugees, have been refused entry to Australia, in the last year.[96]
Canada
The Communications Security Establishment Canada (CSEC) offers the NSA resources for advanced collection, processing, and analysis. It has set up covert sites at the request of NSA.[97] The US-Canada SIGNT relationship dates back to a secret alliance formed during World War II, and was formalized in 1949 under the CANUSA Agreement.[97]
On behalf of the NSA, the CSEC opened secret surveillance facilities in 20 countries around the world.[98]
As well, the Communications Security Establishment Canada has been revealed, following the global surveillance disclosures to be engaging in surveillance on Wifi Hotspots of major Canadian Airports, collecting meta-data to use for engaging in surveillance on travelers, even days after their departure from said airports.[99]
The NSA's relationship with Canada's CSEC
The NSA's relationship with Canada's CSEC
NSA document on a mass surveillance operation with Canada's CSEC agency during the G8 and G20 summits in Toronto in 2010
NSA document on a mass surveillance operation with Canada's CSEC agency during the G8 and G20 summits in Toronto in 2010
Denmark
The Politiets Efterretningstjeneste (PET) of Denmark, a domestic intelligence agency, exchanges data with the NSA on a regular basis, as part of a secret agreement with the United States.[100] Being one of the "9-Eyes" of the UKUSA Agreement, Denmark's relationship with the NSA is closer than the NSA's relationship with Germany, Sweden, Spain, Belgium or Italy.[101]
France
The Directorate-General for External Security (DGSE) of France maintains a close relationship with both the NSA and the GCHQ after discussions for increased cooperation began in November 2006.[102] By the early 2010s, the extent of cooperation in the joint interception of digital data by the DGSE and the NSA was noted to have increased dramatically.[102][103]
In 2011, a formal memorandum for data exchange was signed by the DGSE and the NSA, which facilitated the transfer of millions of metadata records from the DGSE to the NSA.[104] From December 2012 to 8 January 2013, over 70 million metadata records were handed over to the NSA by French intelligence agencies.[104]
Germany
The Bundesnachrichtendienst (BND) of Germany systematically transfers metadata from German intelligence sources to the NSA. In December 2012 alone, the BND provided the NSA with 500 million metadata records.[105] The NSA granted the Bundesnachrichtendienst access to X-Keyscore,[106] in exchange for the German surveillance programs Mira4 and Veras.[105]
In early 2013, Hans-Georg Maaßen, President of the German domestic security agency Bundesamt für Verfassungsschutz (BfV), made several visits to the headquarters of the NSA. According to classified documents of the German government, Maaßen agreed to transfer all data records of persons monitored in Germany by the BfV via XKeyscore to the NSA.[107] In addition, the BfV works very closely with eight other U.S. government agencies, including the CIA.[108] Under Project 6, which is jointly operated by the CIA, BfV, and BND, a massive database containing personal information such as photos, license plate numbers, Internet search histories and telephone metadata was developed to gain a better understanding of the social relationships of presumed jihadists.[109]
In 2012, the BfV handed over 864 data sets of personal information to the CIA, NSA and seven other U.S. intelligence agencies. In exchange, the BND received data from U.S. intelligence agencies on 1,830 occasions. The newly acquired data was handed over to the BfV and stored in a domestically accessible system known as NADIS WN.[110]
The Dagger Complex in Darmstadt, Germany, is operated by the United States Army on behalf of the NSA. Similar to the NSA's Utah Data Center, the Dagger Complex is able to process, store, and decrypt millions of data pieces.[111]
The Dagger Complex in Darmstadt, Germany, is operated by the United States Army on behalf of the NSA. Similar to the NSA's Utah Data Center, the Dagger Complex is able to process, store, and decrypt millions of data pieces.[111]
The Bad Aibling Station in Bavaria, Germany, was operated by the NSA until the early 2000s. It is currently run by the BND. As part of the global surveillance network ECHELON, it is the largest listening post outside Britain and the USA.[112]
The Bad Aibling Station in Bavaria, Germany, was operated by the NSA until the early 2000s. It is currently run by the BND. As part of the global surveillance network ECHELON, it is the largest listening post outside Britain and the USA.[112]
In 2013, the German news magazine Der Spiegel published an excerpt of an NSA document leaked by Snowden, showing that the BND used the NSA's XKEYSCORE to wiretap a German domestic target.
In 2013, the German news magazine Der Spiegel published an excerpt of an NSA document leaked by Snowden, showing that the BND used the NSA's XKEYSCORE to wiretap a German domestic target.
Israel
On 11 September 2013, The Guardian released a secret NSA document leaked by Snowden, which reveals how Israel's Unit 8200 (ISNU) was given raw, unfiltered data of U.S. citizens, as part of a secret agreement with the U.S. National Security Agency.[113]
The Israeli SIGINT National Unit (ISNU) routinely receives raw, unfiltered data of U.S. citizens from the NSA. However, a secret NSA document leaked by Snowden revealed that U.S. government officials are explicitly exempted from such forms of data sharing with the ISNU.[113] As stated in a memorandum detailing the rules of data sharing on U.S. citizens, the ISNU is obligated to:
Destroy upon recognition any communication contained in raw SIGINT provided by NSA that is either to or from an official of the U.S. government. "U.S. government officials" include officials of the Executive Branch (including White House, Cabinet Departments, and independent agencies); the U.S. House of Representatives and Senate (members and staff); and the U.S. Federal Court system (including, but not limited to, the Supreme Court).
— Memorandum of understanding between the NSA and Israel (circa 2009)
According to the undated memorandum, the ground rules for intelligence sharing between the NSA and the ISNU were laid out in March 2009.[113] Under the data sharing agreement, the ISNU is allowed to retain the identities of U.S. citizens (excluding U.S. government officials) for up to a year.[113]
Japan
In 2011, the NSA asked the Japanese government to intercept underwater fibre-optic cables carrying phone and Internet data in the Asia-Pacific region. However, the Japanese government refused to comply.[114]
Libya
Under the reign of Muammar Gaddafi, the Libyan regime forged a partnership with Britain's secret service MI6 and the U.S. Central Intelligence Agency (CIA) to obtain information about Libyan dissidents living in the United States and Canada. In exchange, Gaddafi allowed the Western democracies to use Libya as a base for extraordinary renditions.[115][116][117][118][119]
Netherlands
The Algemene Inlichtingen en Veiligheidsdienst (AIVD) of the Netherlands has been receiving and storing data of Internet users gathered by U.S. intelligence sources such as the NSA's PRISM surveillance program.[120] During a meeting in February 2013, the AIVD and the MIVD briefed the NSA on their attempts to hack Internet forums and to collect the data of all users using a technology known as Computer Network Exploitation (CNE).[121]
Summary of a meeting held in February 2013 between the NSA and the Dutch intelligence services AIVD and MIVD
Summary of a meeting held in February 2013 between the NSA and the Dutch intelligence services AIVD and MIVD
Norway
The Norwegian Intelligence Service (NIS) has confirmed that data collected by the agency is "shared with the Americans".[122] Kjell Grandhagen, head of Norwegian military intelligence told reporters at a news conference that "We share this information with partners, and partners share with us ... We are talking about huge amounts of traffic data".[123]
In cooperation with the NSA, the NIS has gained access to Russian targets in the Kola Peninsula and other civilian targets. In general, the NIS provides information to the NSA about "Politicians", "Energy" and "Armament".[124] A top secret memo of the NSA lists the following years as milestones of the Norway-United States of America SIGNT agreement, or NORUS Agreement:
1952 – Informal starting year of cooperation between the NIS and the NSA[125]
1954 – Formalization of the NORUS Agreement[125]
1963 – Extension of the agreement for coverage of foreign instrumentation signals intelligence (FISINT)[125]
1970 – Extension of the agreement for coverage of electronic intelligence (ELINT)[125]
1994 – Extension of the agreement for coverage of communications intelligence (COMINT)[125]
The NSA perceives the NIS as one of its most reliable partners. Both agencies also cooperate to crack the encryption systems of mutual targets. According to the NSA, Norway has made no objections to its requests.[125]
Singapore
The Defence Ministry of Singapore and its Security and Intelligence Division (SID) have been secretly intercepting much of the fibre optic cable traffic passing through the Asian continent. In close cooperation with the Australian Signals Directorate (ASD/DSD), Singapore's SID has been able to intercept SEA-ME-WE 3 (Southeast Asia-Middle East-Western Europe 3) as well as SEA-ME-WE 4 telecommunications cables.[95] Access to these international telecommunications channels is facilitated by Singapore's government-owned operator, SingTel.[95] Temasek Holdings, a multibillion-dollar sovereign wealth fund with a majority stake in SingTel, has maintained close relations with the country's intelligence agencies.[95]
Information gathered by the Government of Singapore is transferred to the Government of Australia as part of an intelligence sharing agreement. This allows the "Five Eyes" to maintain a "stranglehold on communications across the Eastern Hemisphere".[85]
Spain
In close cooperation with the Centro Nacional de Inteligencia (CNI), the NSA intercepted 60.5 million phone calls in Spain in a single month.[126][127]
Sweden
The Försvarets radioanstalt (FRA) of Sweden (codenamed Sardines)[128] has allowed the "Five Eyes" to access underwater cables in the Baltic Sea.[128] On 5 December 2013, Sveriges Television (Swedish Television) revealed that the FRA has been conducting a clandestine surveillance operation targeting the internal politics of Russia. The operation was conducted on behalf of the NSA, which receives data handed over to it by the FRA.[129][130]
According to documents leaked by Snowden, the FRA of Sweden has been granted access to the NSA's international surveillance program XKeyscore.[131]
The NSA's relationship with Sweden's FRA under the UKUSA Agreement
The NSA's relationship with Sweden's FRA under the UKUSA Agreement
Switzerland
The Federal Intelligence Service (NDB) of Switzerland exchanges information with the NSA regularly, on the basis of a secret agreement to circumvent domestic surveillance restrictions.[132][133] In addition, the NSA has been granted access to Swiss surveillance facilities in Leuk (canton of Valais) and Herrenschwanden (canton of Bern), which are part of the Swiss surveillance program Onyx.[132]
According to the NDB, the agency maintains working relationships with about 100 international organizations. However, the NDB has denied any form of cooperation with the NSA.[134] Although the NSA does not have direct access to Switzerland's Onyx surveillance program, the Director of the NDB acknowledged that it is possible for other U.S. intelligence agencies to gain access to Switzerland's surveillance system.[134]
United Kingdom
See also: Mass surveillance in the United Kingdom
The British government allowed the NSA to store personal data of British citizens.[135]
Under Project MINARET, anti-Vietnam War dissidents in the United States were jointly targeted by the GCHQ and the NSA.[136][137]
RAF Menwith Hill, near Harrogate, North Yorkshire, is the biggest listening post outside the United States. It was used by U.S. military personnel to spy on Britons on behalf of MI5 and MI6.[138]
RAF Menwith Hill, near Harrogate, North Yorkshire, is the biggest listening post outside the United States. It was used by U.S. military personnel to spy on Britons on behalf of MI5 and MI6.[138]
United States
National Security Agency surveillance
Map of global NSA data collection as of 2007, with countries subject to the most data collection shown in red
Programs
Legislation
Institutions
Lawsuits
Whistleblowers
Publication
Related
Concepts
Collaboration
vte
See also: Mass surveillance in the United States
Central Intelligence Agency (CIA)
The CIA pays AT&T more than US$10 million a year to gain access to international phone records, including those of U.S. citizens.[139]
National Security Agency (NSA)
The NSA's Foreign Affairs Directorate interacts with foreign intelligence services and members of the Five Eyes to implement global surveillance.[140]
Federal Bureau of Investigation (FBI)
The FBI acts as the liaison between U.S. intelligence agencies and Silicon Valley giants such as Microsoft.[44]
Department of Homeland Security (DHS)
In the early 2010s, the DHS conducted a joint surveillance operation with the FBI to crack down on dissidents of the Occupy Wall Street protest movement.[141][142][143]
Other law enforcement agencies
The NSA supplies domestic intercepts to the Drug Enforcement Administration (DEA), Internal Revenue Service (IRS), and other law enforcement agencies, who use intercepted data to initiate criminal investigations against US citizens. Federal agents are instructed to "recreate" the investigative trail in order to "cover up" where the information originated.[32]
White House
Duration: 33 seconds.0:33Subtitles available.CC
U.S. President Barack Obama emphasizing the importance of global surveillance to prevent terrorist attacks
Weeks after the September 11 attacks, U.S. President George W. Bush signed the Patriot Act to ensure no disruption in the government's ability to conduct global surveillance:
This new law that I sign today will allow surveillance of all communications used by terrorists, including e-mails, the Internet and cell phones.
— U.S. President George W. Bush on the implementation of the Patriot Act after the September 11 attacks[144]
The Patriot Act was extended by U.S. President Barack Obama in May 2011 to further extend the federal government's legal authority to conduct additional forms of surveillance such as roving wiretaps.[145]
Commercial cooperation
Over 70 percent of the United States Intelligence Community's budget is earmarked for payment to private firms.[146] According to Forbes magazine, the defense technology company Lockheed Martin is currently the US's biggest defense contractor, and it is destined to be the NSA's most powerful commercial partner and biggest contractor in terms of dollar revenue.[147]
AT&T
In a joint operation with the NSA, the American telecommunications corporation AT&T operates Room 641A in the SBC Communications building in San Francisco to spy on Internet traffic.[148] The CIA pays AT&T more than US$10 million a year to gain access to international phone records, including those of U.S. citizens.[139]
Booz Allen Hamilton
Projects developed by Booz Allen Hamilton include the Strategic Innovation Group to identify terrorists through social media, on behalf of government agencies.[149] During the fiscal year of 2013, Booz Allen Hamilton derived 99% of its income from the government, with the largest portion of its revenue coming from the U.S. Army.[149] In 2013, Booz Allen Hamilton was hailed by Bloomberg Businessweek as "the World's Most Profitable Spy Organization".[150]
British Telecommunications
British Telecommunications (code-named Remedy[151]), a major supplier of telecommunications, granted Britain's intelligence agency GCHQ "unlimited access" to its network of undersea cables, according to documents leaked by Snowden.[151]
Microsoft
The American multinational corporation Microsoft helped the NSA to circumvent software encryption safeguards. It also allowed the federal government to monitor web chats on the Outlook.com portal.[44] In 2013, Microsoft worked with the FBI to allow the NSA to gain access to the company's cloud storage service SkyDrive.[44]
Orange S.A.
French telecommunications corporation Orange S.A. shares customer call data with intelligence agencies.[152]
The French telecommunications corporation Orange S.A. shares customer call data with the French intelligence agency DGSE, and the intercepted data is handed over to GCHQ.[152]
RSA Security
RSA Security was paid US$10 million by the NSA to introduce a cryptographic backdoor in its encryption products.[153]
Stratfor
Strategic Forecasting, Inc., more commonly known as Stratfor, is a global intelligence company offering information to governments and private clients including Dow Chemical Company, Lockheed Martin, Northrop Grumman, Raytheon, the U.S. Department of Homeland Security, the U.S. Defense Intelligence Agency, and the U.S. Marine Corps.[154]
Vodafone
The British telecommunications company Vodafone (code-named Gerontic[151]) granted Britain's intelligence agency GCHQ "unlimited access" to its network of undersea cables, according to documents leaked by Snowden.[151]
In-Q-Tel
In-Q-Tel, which receives more than US$56 million a year in government support,[155] is a venture capital firm that enables the CIA to invest in Silicon Valley.[155]
Palantir Technologies
Palantir Technologies is a data mining corporation with close ties to the FBI, NSA and CIA.[156][157]
Based in Palo Alto, California, the company developed a data collection and analytical program known as Prism.[158][159]
In 2011, it was revealed that the company conducted surveillance on Glenn Greenwald.[160][161]
Surveillance evasion
Several countries have evaded global surveillance by constructing secret bunker facilities deep below the Earth's surface.[162]
North Korea
Despite North Korea being a priority target, the NSA's internal documents acknowledged that it did not know much about Kim Jong-un and his regime's intentions.[69]
Iran
In October 2012, Iran's police chief Esmail Ahmadi Moghaddam alleged that Google is not a search engine but "a spying tool" for Western intelligence agencies.[163] Six months later in April 2013, the country announced plans to introduce an "Islamic Google Earth" to evade global surveillance.[164]
Libya
Libya evaded surveillance by building "hardened and buried" bunkers at least 40 feet below ground level.[162]
Impact
Main article: Aftermath of the global surveillance disclosures
"Stop Watching Us" rally in Berlin, Germany, August 2014
The global surveillance disclosure has caused tension in the bilateral relations of the United States with several of its allies and economic partners as well as in its relationship with the European Union. On 12 August 2013, President Obama announced the creation of an "independent" panel of "outside experts" to review the NSA's surveillance programs. The panel is due to be established by the Director of National Intelligence, James R. Clapper, who will consult and provide assistance to them.[165]
According to a survey undertaken by the human rights group PEN International, these disclosures have had a chilling effect on American writers. Fearing the risk of being targeted by government surveillance, 28% of PEN's American members have curbed their usage of social media, and 16% have self-censored themselves by avoiding controversial topics in their writings.[166]
Gallery
According to Snowden's documents, the United Nations Headquarters and the United Nations General Assembly were targeted by NSA employees disguised as diplomats.[72]
According to Snowden's documents, the United Nations Headquarters and the United Nations General Assembly were targeted by NSA employees disguised as diplomats.[72]
Citing Snowden's documents, The Guardian reported that British officials had set up fake Internet cafes at the 2009 G-20 London summit to spy on the delegates' use of computers, and to install key-logging software on the delegates' phones. This allowed British representatives to gain a "negotiating advantage" at the summit.[167]
Citing Snowden's documents, The Guardian reported that British officials had set up fake Internet cafes at the 2009 G-20 London summit to spy on the delegates' use of computers, and to install key-logging software on the delegates' phones. This allowed British representatives to gain a "negotiating advantage" at the summit.[167]
According to Snowden's interview with the South China Morning Post, the U.S. government has been hacking numerous non-military targets in China for years. Other high-priority targets include academic institutions such as the prestigious Tsinghua University in Beijing.[168]
According to Snowden's interview with the South China Morning Post, the U.S. government has been hacking numerous non-military targets in China for years. Other high-priority targets include academic institutions such as the prestigious Tsinghua University in Beijing.[168]
The Council of the European Union, with its headquarters at the Justus Lipsius building in Brussels, was targeted by NSA employees working near the headquarters of NATO. An NSA document dated September 2010 explicitly names the Europeans as a "location target".[169]
The Council of the European Union, with its headquarters at the Justus Lipsius building in Brussels, was targeted by NSA employees working near the headquarters of NATO. An NSA document dated September 2010 explicitly names the Europeans as a "location target".[169]
The reservations system of Russia's Aeroflot airline was hacked by the NSA.[170]
The reservations system of Russia's Aeroflot airline was hacked by the NSA.[170]
Petrobras, currently the world's leader in offshore deepwater drilling, is a "prominent" target of the U.S. government.[171]
Petrobras, currently the world's leader in offshore deepwater drilling, is a "prominent" target of the U.S. government.[171]
From 2002 to 2013, the German Chancellor Angela Merkel was targeted by the U.S. Special Collection Service.[172]
From 2002 to 2013, the German Chancellor Angela Merkel was targeted by the U.S. Special Collection Service.[172]
Israeli Prime Minister Ehud Olmert (pictured) and Defense Minister Ehud Barak were included in a list of surveillance targets used by the GCHQ and the NSA.[173]
Israeli Prime Minister Ehud Olmert (pictured) and Defense Minister Ehud Barak were included in a list of surveillance targets used by the GCHQ and the NSA.[173]
Joaquín Almunia, who served as the European Commissioner for Competition and the Vice-President of the European Commission, was targeted by Britain's GCHQ agency.[76]
Joaquín Almunia, who served as the European Commissioner for Competition and the Vice-President of the European Commission, was targeted by Britain's GCHQ agency.[76]
Indonesia's President Susilo Bambang Yudhoyono and his wife were placed under surveillance by the Australian Signals Directorate (ASD).[174] During the 2007 United Nations Climate Change Conference in Bali, the ASD cooperated with the NSA to conduct mass surveillance on the Indonesian hosts.[175]
Indonesia's President Susilo Bambang Yudhoyono and his wife were placed under surveillance by the Australian Signals Directorate (ASD).[174] During the 2007 United Nations Climate Change Conference in Bali, the ASD cooperated with the NSA to conduct mass surveillance on the Indonesian hosts.[175]
The video gaming network Xbox Live was placed under surveillance to unravel possible terrorist plots.[176]
The video gaming network Xbox Live was placed under surveillance to unravel possible terrorist plots.[176]
See also
World portal
2013 Department of Justice investigations of reporters
Cyber spying
Terrorist Finance Tracking Program
Top Secret America
References
Webb, Maureen (2007). Illusions of Security: Global Surveillance and Democracy in the Post-9/11 World (1st ed.). San Francisco: City Lights Books. ISBN 978-0872864764.
Zevenbergen, Bendert (3 December 2013). "Adventures in digital surveillance". European View. 12 (2): 223–233. doi:10.1007/s12290-013-0287-x. "Snowden used the press to inform the world that a global surveillance state may be being built. This led to the beginning of a global political debate on digital communications surveillance."
Ranger, Steve (24 March 2015). "The undercover war on your internet secrets: How online surveillance cracked our trust in the web". TechRepublic. Archived from the original on 12 June 2016. Retrieved 12 June 2016.
Pfluke, Corey (4 July 2019). "A history of the Five Eyes Alliance: Possibility for reform and additions". Comparative Strategy. 38 (4): 302–315. doi:10.1080/01495933.2019.1633186. ISSN 0149-5933. S2CID 202317080.
"Q&A: What you need to know about Echelon". BBC. 29 May 2001.
Nabbali, Talitha; Perry, Mark (March 2004). "Going for the throat". Computer Law & Security Review. 20 (2): 84–97. doi:10.1016/S0267-3649(04)00018-4. "It wasn't until 1971 that the UKUSA allies began ECHELON"
"Pre-Emption - The Nsa And The Telecoms - Spying On The Home Front - FRONTLINE - PBS". pbs.org. Retrieved 8 March 2015.
Cohen, Martin (2006). No Holiday. New York: Disinformation Company Ltd. ISBN 978-1-932857-29-0.
Peggy Becker (October 1999). DEVELOPMENT OF SURVEILLANCE TECHNOLOGY AND RISK OF ABUSE OF ECONOMIC INFORMATION (Report). STOA, European Parliament. Retrieved 31 January 2014.
"Snowden has 'thousands' of damaging NSA documents, says Greenwald". MSNBC. 15 July 2013. Retrieved 8 March 2015.
Glenn Greenwald; Ewen MacAskill (8 June 2013). "Boundless Informant: the NSA's secret tool to track global surveillance data". The Guardian. London. Retrieved 12 June 2013.
"Senators: Limit NSA snooping into US phone records". Associated Press. Archived from the original on 29 October 2013. Retrieved 15 October 2013. ""Is it the goal of the NSA to collect the phone records of all Americans?" Udall asked at Thursday's hearing. "Yes, I believe it is in the nation's best interest to put all the phone records into a lockbox that we could search when the nation needs to do it. Yes," Alexander replied."
Siobhan Gorman. "Meltdowns Hobble NSA Data Center". The Wall Street Journal. Retrieved 19 October 2013. "The Utah facility, one of the Pentagon's biggest U.S. construction projects, has become a symbol of the spy agency's surveillance prowess, which gained broad attention in the wake of leaks from NSA contractor Edward Snowden."
Shane Harris (22 August 2012). "Who's Watching the N.S.A Watchers?". The New York Times. Retrieved 25 December 2013.
Duran-Sanchez, Mabel (10 August 2013). "Greenwald Testifies to Brazilian Senate about NSA Espionage Targeting Brazil and Latin America". Retrieved 13 August 2013.
"Glenn Greenwald afirma que documentos dizem respeito à interesses comerciais do governo americano". 6 August 2013. Retrieved 13 August 2013.
How Microsoft handed the NSA access to encrypted messages, The Guardian, 12 July 2013. Retrieved 13 July 2013.
Bridie Jabour in Sydney (12 July 2013). "Telstra signed deal that would have allowed US spying". The Guardian. London.
The first three days of revelations were: the FISC court order that Verizon provide bulk metadata to its customers to the NSA; presentation slides explaining the cooperation of nine US internet giants through the PRISM program; and the bulk collection of Chinese users' text messages, which coincided with Xi Jinping's visit to California to meet Barack Obama.
Shorrock, Tim (15 April 2013). "The Untold Story: Obama's Crackdown on Whistleblowers: The NSA Four reveal how a toxic mix of cronyism and fraud blinded the agency before 9/11". The Nation.
JAMES RISEN; ERIC LICHTBLAU (16 December 2005). "Bush Lets U.S. Spy on Callers Without Courts". The New York Times.
Leslie Cauley (11 May 2006). "NSA has massive database of Americans' phone calls". USA Today.
Poulsen, Kevin (6 March 2008). "Whistle-Blower: Feds Have a Backdoor Into Wireless Carrier – Congress Reacts". Wired. Retrieved 14 August 2013.
Maass, Peter (18 August 2013). "How Laura Poitras Helped Snowden Spill His Secrets". The New York Times.
Laura Poitras; Marcel Rosenbach; Holger Stark (12 August 2013). "Ally and Target: US Intelligence Watches Germany Closely". Der Spiegel. Retrieved 13 August 2013.
DeYoung, Karen (12 August 2013). "Colombia asks Kerry to explain NSA spying". The Washington Post. Retrieved 13 August 2013.
"Greenwald diz que espionagem dá vantagens comerciais e industriais aos Estados Unidos" (in Portuguese). Federal Senate of Brazil. Retrieved 13 August 2013.
"Greenwald diz que EUA espionam para obter vantagens comerciais" (in Portuguese). Deutsche Welle. Retrieved 13 August 2013.
"Snowden: NSA's indiscriminate spying 'collapsing' - The Washington Post". Archived from the original on 17 December 2013.
"NSA program stopped no terror attacks, says White House panel member".
Finn, Peter (28 June 2013). "National Security". The Washington Post.
"Exclusive: U.S. directs agents to cover up program used to investigate Americans". Reuters. 5 August 2013. Retrieved 14 August 2013.
"Senators: Limit NSA snooping into US phone records". Associated Press. Archived from the original on 29 October 2013. Retrieved 15 October 2013.
John Miller. "NSA speaks out on Snowden, spying". CBS News. Retrieved 17 December 2013. "What they are doing is collecting the phone records of more than 300 million Americans."
Greenwald, Glenn (31 July 2013)."XKeyscore: NSA tool collects 'nearly everything a user does on the internet' – XKeyscore Gives 'Widest-Reaching' Collection of Online Data – NSA Analysts Require No Prior Authorization for Searches – Sweeps Up Emails, Social Media Activity and Browsing History". The Guardian. Retrieved 1 August 2013.
Nakashima, Ellen (31 July 2013). "Newly declassified documents on phone records program released". The Washington Post. Retrieved 4 August 2013.
Charlie Savage; David E. Sanger (31 July 2013). "Senate Panel Presses N.S.A. on Phone Logs". The New York Times. Retrieved 4 August 2013.
Ball, James (25 October 2013). "Leaked memos reveal GCHQ efforts to keep mass surveillance secret". The Guardian. Retrieved 25 October 2013.
Gellman, Barton; Poitras, Laura (6 June 2013). "US Intelligence Mining Data from Nine U.S. Internet Companies in Broad Secret Program". The Washington Post. Retrieved 15 June 2013.
"Documents on N.S.A. Efforts to Diagram Social Networks of U.S. Citizens". The New York Times. 28 September 2013. Retrieved 17 December 2013.
James Risen; Laura Poitras (28 September 2013). "N.S.A. Gathers Data on Social Connections of U.S. Citizens". The New York Times. Retrieved 30 September 2013.
Segal, Aaron; Feigenbaum, Joan; Ford, Bryan (24 October 2016). "Privacy-Preserving Lawful Contact Chaining: [Preliminary Report]". Proceedings of the 2016 ACM on Workshop on Privacy in the Electronic Society. WPES '16. New York, NY, USA: Association for Computing Machinery. pp. 185–188. doi:10.1145/2994620.2994628. ISBN 978-1-4503-4569-9.
Barton Gellman; Ashkan Soltani (1 November 2013). "NSA collects millions of e-mail address books globally". The Washington Post. Retrieved 20 December 2013.
Glenn Greenwald; Ewen MacAskill; Laura Poitras; Spencer Ackerman; Dominic Rushe. "Microsoft handed the NSA access to encrypted messages". The Guardian. Retrieved 22 December 2013.
"'Follow the Money': NSA Spies on International Payments". Der Spiegel. Retrieved 23 October 2013.
Barton Gellman; Ashkan Soltani (4 December 2013). "NSA tracking cellphone locations worldwide, Snowden documents show". The Washington Post. Retrieved 5 December 2013.
"How the NSA is tracking people right now". The Washington Post. 4 December 2013. Retrieved 6 December 2013.
Ashkan Soltani; Matt DeLong (4 December 2013). "FASCIA: The NSA's huge trove of location records". The Washington Post. Retrieved 6 December 2013.
"How the NSA uses cellphone tracking to find and 'develop' targets". The Washington Post. 4 December 2013. Retrieved 6 December 2013.
"Reporter explains NSA collection of cellphone data". The Washington Post. 4 December 2013. Retrieved 6 December 2013.
Peterson, Andrea (4 December 2013). "The NSA says it 'obviously' can track locations without a warrant. That's not so obvious". The Washington Post's The Switch. Retrieved 6 December 2013.
Lee, Timothy (4 December 2013). "The NSA could figure out how many Americans it's spying on. It just doesn't want to". The Washington Post's The Switch. Retrieved 6 December 2013.
Craig Timberg; Ashkan Soltani. "By cracking cellphone code, NSA has capacity for decoding private conversations". The Washington Post. Retrieved 14 December 2013.
"How the NSA pinpoints a mobile device". The Washington Post. Retrieved 14 December 2013.
Laura Poitras; Marcel Rosenbach; Holger Stark. "iSpy: How the NSA Accesses Smartphone Data". Der Spiegel. Retrieved 9 September 2013.
Gellman, Barton; Soltani, Ashkan (30 October 2013). "NSA infiltrates links to Yahoo, Google data centers worldwide, Snowden documents say". The Washington Post. Retrieved 31 October 2013.
Gellman, Barton; Soltani, Ashkan; Peterson, Andrea (4 November 2013). "How we know the NSA had access to internal Google and Yahoo cloud data". The Washington Post. Retrieved 5 November 2013.
Barton Gellman; Craig Timberg; Steven Rich (4 October 2013). "Secret NSA documents show campaign against Tor encrypted network". The Washington Post. Retrieved 19 November 2013.
Steven Rich; Matt DeLong (4 October 2013). "NSA slideshow on 'The TOR problem'". The Washington Post. Retrieved 19 November 2013.
Lee, Timothy B. (4 October 2013). "Everything you need to know about the NSA and Tor in one FAQ". The Washington Post. Retrieved 19 November 2013.
"NSA report on the Tor encrypted network". The Washington Post. 4 October 2013. Retrieved 19 November 2013.
"GCHQ report on 'MULLENIZE' program to 'stain' anonymous electronic traffic". The Washington Post. 4 October 2013. Retrieved 19 November 2013.
James Ball; Bruce Schneier; Glenn Greenwald (4 October 2013). "NSA and GCHQ target Tor network that protects anonymity of web users". The Guardian. Retrieved 19 November 2013.
Schneier, Bruce (4 October 2013). "Attacking Tor: how the NSA targets users' online anonymity". The Guardian. Retrieved 19 November 2013.
"'Tor Stinks' presentation – read the full document". The Guardian. 4 October 2013. Retrieved 19 November 2013.
"Tor: 'The king of high-secure, low-latency anonymity'". The Guardian. 4 October 2013. Retrieved 19 November 2013.
Laura Poitras; Marcel Rosenbach; Holger Stark (17 November 2013). "'Royal Concierge': GCHQ Monitors Hotel Reservations to Track Diplomats". Der Spiegel. Retrieved 17 November 2013.
MARK MAZZETTI; JUSTIN ELLIOTT (9 December 2013). "Spies Infiltrate a Fantasy Realm of Online Games". The New York Times. Retrieved 12 December 2013.
Barton Gellman; Greg Miller (29 August 2013). "U.S. spy network's successes, failures and objectives detailed in 'black budget' summary". The Washington Post. Retrieved 29 August 2013.
Maass, Peter (13 August 2013). "How Laura Poitras Helped Snowden Spill His Secrets". The New York Times. Retrieved 13 August 2013.
Easley, Jonathan. "Snowden: NSA targeted journalists critical of government after 9/11". The Hill. Retrieved 14 August 2013.
Laura Poitras; Marcel Rosenbach; Holger Stark (26 August 2013). "Codename 'Apalachee': How America Spies on Europe and the UN". Der Spiegel. p. 2. Retrieved 26 August 2013.
Laura Poitras; Marcel Rosenbach; Fidelius Schmid; Holger Stark (29 June 2013). "Attacks from America: NSA Spied on European Union Offices". Der Spiegel. Retrieved 26 August 2013.
"Report: Canada spies targeted Brazil mine ministry". Associated Press. Archived from the original on 10 October 2013. Retrieved 7 October 2013.
"'Success Story': NSA Targeted French Foreign Ministry". Der Spiegel. Retrieved 24 September 2013.
James Ball; Nick Hopkins. "GCHQ and NSA targeted charities, Germans, Israeli PM and EU chief". The Guardian. Retrieved 20 December 2013.
Glenn Greenwald; Stefania Maurizi (5 December 2013). "Revealed: How the Nsa Targets Italy". L'espresso. Retrieved 13 December 2013.
Shobhan Saxena (25 September 2013). "NSA planted bugs at Indian missions in D.C., U.N." The Hindu. Chennai, India. Retrieved 24 September 2013.
Jens Glüsing; Laura Poitras; Marcel Rosenbach; Holger Stark. "Fresh Leak on US Spying: NSA Accessed Mexican President's Email". Der Spiegel. Retrieved 20 October 2013.
Laura Poitras, Marcel Rosenbach, Fidelius Schmid und Holger Stark (29 June 2013). "Geheimdokumente: NSA horcht EU-Vertretungen mit Wanzen aus". Der Spiegel (in German). Retrieved 29 June 2013.
"US-Geheimdienst hörte Zentrale der Vereinten Nationen ab". Der Spiegel (in German). 25 August 2013. Retrieved 25 August 2013.
U.S. National Security Agency. Early Papers Concerning US-UK Agreement – 1940–1944 Archived 18 September 2013 at the Wayback Machine. Agreement between British Government Code and Cipher School and U.S. War Department dated 17 May 1943. Retrieved: 5 October 2013.
Norton-Taylor, Richard (25 June 2010). "Not so secret: deal at the heart of UK-US intellig
-
 45:29
45:29
The Memory Hole
26 days agoHow a Washington Assassination Brought Pinochet's Terror State to Justice (2019)
6382 -
 16:18
16:18
RealitySurvival
21 hours agoService & Sacrifice Are Required For Victory
14.6K3 -
 LIVE
LIVE
Total Horse Channel
23 hours ago2024 IRCHA Futurity Derby & Horse Show | November 2nd
464 watching -
 13:31
13:31
Tactical Advisor
5 hours agoLegal Glock Switch | Franklin Armory G-S173
44.6K27 -
 17:10
17:10
Clownfish TV
16 hours agoTwitch Political Warning Label Drama Could END Twitch?
32.9K12 -
 8:20
8:20
CarlCrusher
22 hours agoUFO Alien Base Hiding under Secret Mountain Sedona Arizona says Danny Sheehan - Bradshaw Ranch
40.4K5 -
 50:49
50:49
PMG
21 hours ago $11.85 earned"They're Vaccinating Our Food Supply with DNA - Tom Renz"
34.3K11 -
 56:54
56:54
Uncommon Sense In Current Times
14 hours ago $6.83 earned"Reclaiming Our Voice: A Christian Perspective on Politics and Parenting With John DeBerry"
34.5K3 -
 59:27
59:27
Trumpet Daily
1 day ago $10.05 earnedDesperate Dems: Trump Supporters Are Dumb, Deplorable Garbage Trumpet Daily | Nov. 1, 2024
34.3K26 -
 5:51
5:51
Memology 101
13 hours ago $4.66 earnedCNBC anchor OBLITERATES NJ Governor as he FAILS to elaborate a single policy he likes from Kamala
26.6K38