Premium Only Content
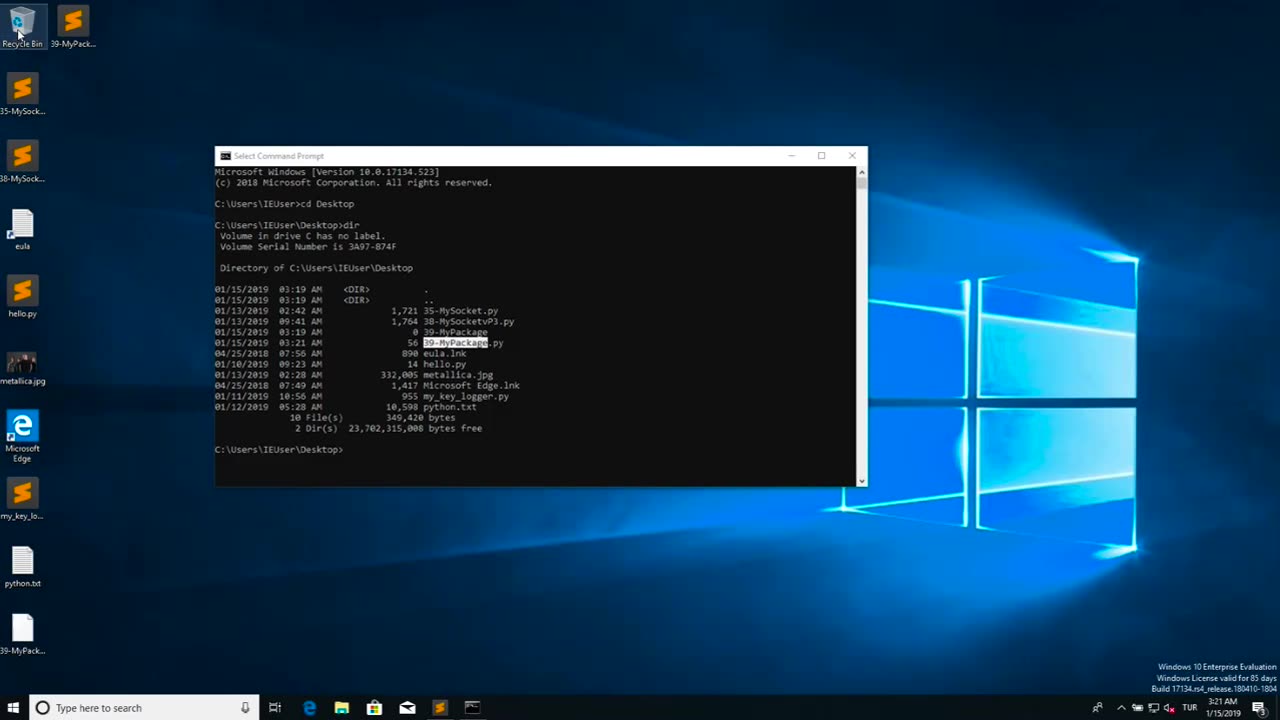
Chapter-39, LEC-2 | Malicious Files | #ethicalhacking #maliciousdiles #hacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Malicious files refer to digital files, such as software programs or documents, that are intentionally designed to harm or compromise the security of a computer, network, or device. These files may contain malicious code, also known as malware, which can be executed or triggered to perform malicious activities without the knowledge or consent of the user.
Malicious files can come in various forms, including viruses, worms, Trojans, ransomware, spyware, adware, and other types of malware. They are typically disguised as legitimate files or software to deceive users into downloading or executing them. Once the malicious file is executed or opened, it can spread throughout the system, exploit vulnerabilities, steal sensitive information, disrupt operations, or cause other types of damage.
Malicious files are often distributed through various means, such as infected email attachments, compromised websites, infected USB drives, social engineering tactics, and other methods. They can target any type of device or operating system, including computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
The consequences of encountering and executing malicious files can be severe, ranging from data breaches and financial loss to privacy violations, system downtime, and reputational damage. Therefore, it is crucial to implement robust cybersecurity measures, such as using antivirus software, keeping software and systems updated, being cautious while downloading or opening files, and practicing safe online behavior, to protect against malicious files and other cyber threats.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 UPCOMING
UPCOMING
BonginoReport
1 hour agoVictory Over Marxism: BLM Plaza Falls (Ep.157) - 03/11/2025
4.11K2 -
 LIVE
LIVE
Dear America
10 hours agoMassive Cyberattack Against Elon's X Sparks Widespread CONCERN! + More Attacks On Tesla Vehicles?!
5,556 watching -
 LIVE
LIVE
Wendy Bell Radio
4 hours agoOver The Target
9,620 watching -
 LIVE
LIVE
Bitcoin Policy Institute
39 minutes agoBitcoin for America
539 watching -
 34:43
34:43
Degenerate Jay
22 hours ago $1.02 earnedAssassin's Creed Was Always Anti-Religion?
6.64K4 -
 6:41
6:41
Silver Dragons
18 hours agoCanadian Silver Maple Leaf Coins - Dealer Reveals Everything You NEED to Know
3.73K2 -
 8:42
8:42
Dangerous Freedom
16 hours ago $0.85 earnedThe M&P Competitor SHREDS—But Did Smith & Wesson Screw It Up?
6.69K2 -
 1:12:50
1:12:50
MTNTOUGH Fitness Lab
16 hours agoSTOP Living in Fear: Why Some People Rise From Tragedy AND OTHERS DON'T | Ryan Manion
4.32K -
 8:03
8:03
Alabama Arsenal
1 day ago $0.34 earnedWoox Bravado | Modern Features Meet Timeless Style
8.11K1 -
 2:49:10
2:49:10
TimcastIRL
13 hours agoElon Musk Says X Hit By MASSIVE Cyberattack From Ukraine, Rumble Hit Too w/Ben Davidson| Timcast IRL
246K132