Premium Only Content
Chapter-38, LEC-13 | Getting Contents | #ethicalhacking #content #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
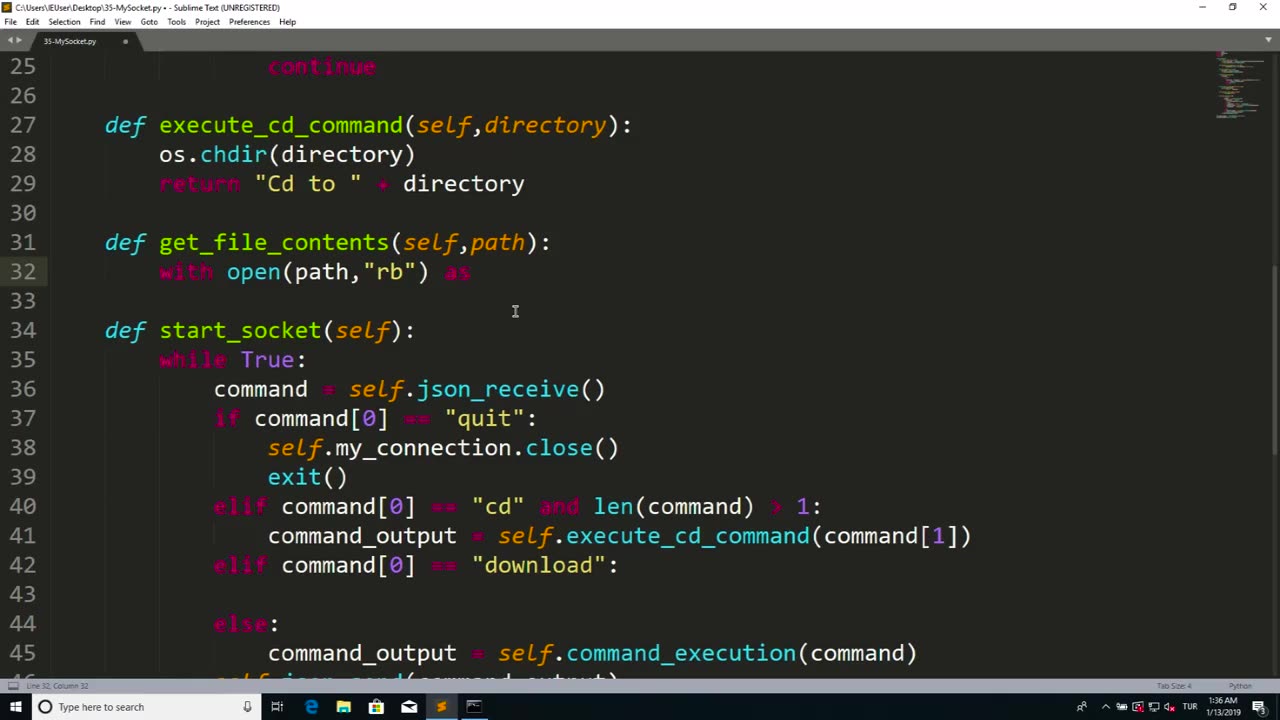
"Getting Contents" is a general term that refers to the process of retrieving data or information from a source, such as a file, a database, a web page, or an API. The implementation of "Getting Contents" may vary depending on the specific source or technology being used.
Here's a general description of how "Getting Contents" can be implemented:
Identifying the source: The first step in getting contents is identifying the source from which the data or information needs to be retrieved. This may involve specifying the file path, the database connection details, the URL of a web page, or the endpoint of an API.
Establishing a connection: Once the source is identified, the implementation of "Getting Contents" may involve establishing a connection to the source. This may involve opening a file, establishing a database connection, making an HTTP request to a web page, or creating a connection to an API.
Retrieving data: After establishing a connection, the implementation of "Getting Contents" typically involves retrieving the data or information from the source. This may involve reading the contents of a file, executing queries to retrieve data from a database, making GET requests to retrieve data from a web page, or calling API endpoints to fetch data.
Parsing or processing data: Once the data is retrieved, the implementation of "Getting Contents" may involve parsing or processing the data to extract the relevant information or transform it into a desired format. This may involve parsing JSON, XML, CSV, or other data formats, extracting data from HTML pages, or processing data from APIs.
Handling errors and exceptions: The implementation of "Getting Contents" should include proper error handling and exception management to handle cases where the data retrieval process fails due to various reasons, such as invalid source, network errors, authentication issues, or data format errors. This may involve checking for error codes, handling exceptions, and providing appropriate error messages or fallback mechanisms.
Closing connections: Once the data retrieval process is complete, the implementation of "Getting Contents" may involve closing the connections or releasing any resources that were acquired during the process, such as closing files, closing database connections, or releasing network resources.
Using retrieved data: Finally, the retrieved data can be used for further processing, analysis, display, or other purposes as needed by the specific use case or application.
The implementation of "Getting Contents" can vary greatly depending on the source, technology, and specific requirements of the task. It may involve various steps such as identifying the source, establishing connections, retrieving data, parsing or processing data, handling errors, and using the retrieved data for further purposes. Proper implementation should include error handling, resource management, and adherence to relevant coding standards or best practices to ensure efficient and reliable functionality.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
Russell Brand
2 hours agoWho Ordered the Hit on Russia’s General Krylov? - SF516
8,448 watching -
 LIVE
LIVE
Dr Disrespect
1 hour ago🔴LIVE - DR DISRESPECT - MARVEL RIVALS - RANKED
4,672 watching -
 LIVE
LIVE
The Charlie Kirk Show
42 minutes agoThe CR Quagmire + An Hour of PBD + Catholic in Hollywood | Davis, Patrick Bet David, Rep. Burlison
6,817 watching -
 LIVE
LIVE
Grant Stinchfield
38 minutes agoDon't Focus on the Drones... Focus on the Mysterious Floating Orbs!
468 watching -
 LIVE
LIVE
The Dana Show with Dana Loesch
35 minutes agoSPENDING BATTLE COUNTDOWN | The Dana Show LIVE On Rumble!
386 watching -
 59:38
59:38
The Dan Bongino Show
3 hours agoThings Have Changed, It's Trump's GOP Now (Ep. 2390) - 12/18/2024
449K712 -
 LIVE
LIVE
Viss
58 minutes ago🔴LIVE - Is Delta Force the Best Casual Extraction Shooter? - Delta Force
204 watching -
 53:22
53:22
The Rubin Report
2 hours agoElon Musk's Major Announcement Reveals His Next Target & It's Huge
27.9K12 -
 2:15:29
2:15:29
Steven Crowder
3 hours ago🔴 The True Cost of Fat Pride: How It's Destroying America
226K122 -
 2:24:25
2:24:25
Matt Kohrs
10 hours agoFed's FOMC Decision Day Chaos || The MK Show
66K3