Premium Only Content
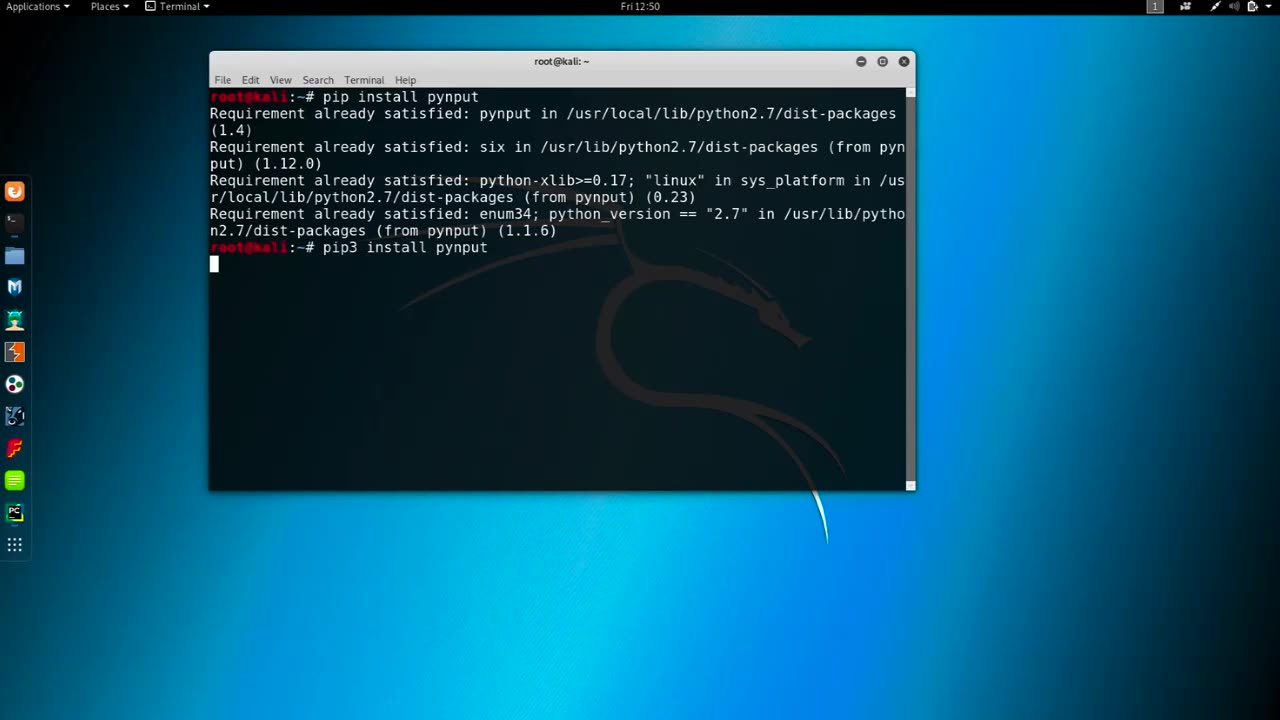
Chapter-37, LEC-4 | Logging Keyboards | #education #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
Logging keyboards, also known as keyboard loggers or keystroke loggers, are software or hardware devices that capture and record all keystrokes made on a computer or mobile device's keyboard. They are used for monitoring or surveillance purposes and can capture every key pressed, including letters, numbers, special characters, and function keys, as well as other activities such as mouse movements, screenshots, and websites visited.
Keyboard loggers can operate in stealth mode, meaning they can run in the background without the user's knowledge or consent, and log all keystrokes made on the device. They can capture a wide range of information, including passwords, usernames, credit card numbers, chat messages, and other sensitive data that is entered using the keyboard.
Keyboard loggers may be used for both legitimate and malicious purposes. Legitimate uses include monitoring employee activity in the workplace, parental control to monitor children's online activities, and data recovery. However, keyboard loggers can also be used maliciously for stealing personal information, committing identity theft, financial fraud, and other cybercrimes.
It is essential to note that using keyboard loggers without proper authorization is illegal in many jurisdictions, and ethical considerations should always be taken into account when using them for any purpose. Users should always be informed and give explicit consent before their activities are monitored, and appropriate security measures should be in place to protect the data collected by keyboard loggers.
It is important to use keyboard loggers responsibly and within the legal and ethical boundaries, ensuring that privacy rights are respected, and data security is maintained at all times. Proper consent, transparency, and compliance with applicable laws and regulations are crucial when using keyboard loggers for any purpose.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 5:17
5:17
BFFs: Dave Portnoy, Josh Richards & Bri Chickenfry
9 days agoSmallest Man
162K20 -
 1:45:03
1:45:03
The Quartering
3 hours agoRFK Big Pharma Meltdown, Alex Jones WIN & Shadow Government To Oppose Trump!
67.8K22 -
 1:53:23
1:53:23
Tucker Carlson
3 hours agoFasting, Prayer, Meditation, & the Global Persecution of Christians (With Hallow CEO Alex Jones)
107K36 -
 53:03
53:03
Ben Shapiro
3 hours agoEp. 2086 - It’s MAHA TIME: Trump Picks RFK Jr.
66K39 -
 57:03
57:03
Russell Brand
6 hours ago“I Can PROVE Biden Took CORRUPT Money From Ukraine” – Rudy Giuliani on The Biden Crime Family –SF494
150K113 -
 1:59:47
1:59:47
The Charlie Kirk Show
4 hours agoRFK's MAHA Agenda + The Trump Border Effect + Will The Senate Confirm? | Kane, Halperin | 11.15.24
149K38 -
 34:45
34:45
Athlete & Artist Show
5 days ago $4.60 earnedNCAA Officially Votes To Allow MAJOR JUNIOR Players!
62.3K3 -
 1:14:55
1:14:55
Mark Kaye
5 hours ago🔴 Is TRUMP the New George Washington of American Politics?
55.8K32 -
 5:40:12
5:40:12
Dcypled
6 hours agoSahkal with my good friend Gabe! | DayZ Adventures
33.8K -
 22:47
22:47
SLS - Street League Skateboarding
7 days agoAll the 9's - SLS Sydney 2024
29.4K