Premium Only Content
Chapter-35, LEC-5 | Getting MAC Address | #rumble #ethicalhacking #hacking #porthacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
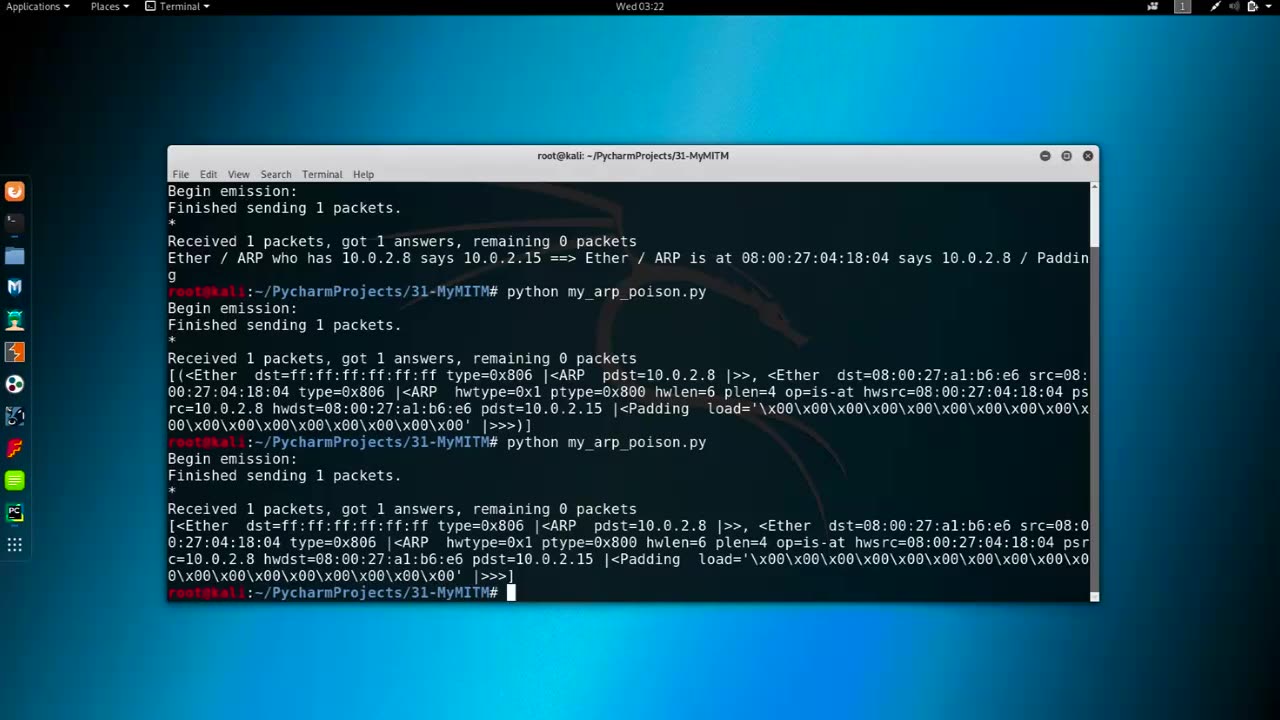
Getting MAC Address refers to the process of obtaining the Media Access Control (MAC) address of a network interface card (NIC) or a network-connected device. The MAC address, also known as the hardware address or physical address, is a unique identifier assigned to the NIC or network interface of a device at the factory, and it is used to uniquely identify a device within a network.
There are several methods to obtain the MAC address of a device:
Command-Line Interface (CLI): Many operating systems, such as Windows, macOS, Linux, and networking devices, provide command-line interfaces (CLI) that allow users to retrieve the MAC address using commands like "ipconfig" (Windows), "ifconfig" (macOS and Linux), or "show interfaces" (networking devices).
Graphical User Interface (GUI): Some operating systems, such as Windows and macOS, provide graphical user interfaces (GUI) that display the MAC address in the network settings or device properties.
Network Configuration or Management Tools: Network configuration or management tools, such as network monitoring software, network scanners, or network inventory tools, may have features to automatically detect and retrieve MAC addresses of devices within a network.
Physical Inspection: On some devices, the MAC address may be printed on a label or engraved on the NIC or device itself, making it possible to physically inspect the device to obtain its MAC address.
Network Protocol: Some network protocols, such as the Address Resolution Protocol (ARP) or the Dynamic Host Configuration Protocol (DHCP), may provide information about MAC addresses during network communication or device registration.
Obtaining MAC addresses can be useful for various networking tasks, such as troubleshooting, network monitoring, network access control, or device identification. However, it's important to note that MAC addresses can be easily spoofed or manipulated, and they should not be solely relied upon for device authentication or security purposes. Other security measures, such as encryption, authentication protocols, and access controls, should also be implemented to secure network communications and protect against unauthorized access.
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
-
 LIVE
LIVE
Matt Kohrs
13 hours agoStocks Bounce, Breaking News & Day Trading Strategy Explained || The MK Show
1,756 watching -
 15:33
15:33
Russell Brand
21 hours agoRemember this?!
173K359 -
 LIVE
LIVE
2 MIKES LIVE
1 hour agoTHE MIKE SCHWARTZ SHOW with DR. MICHAEL J SCHWARTZ 01-02-2025
538 watching -
 6:19
6:19
Rethinking the Dollar
14 hours agoSwiss Chancellery Pushes for Bitcoin: A Revolution in National Finance?
5671 -
 LIVE
LIVE
themidwesterner
38 minutes agoMecosta Co, MI reverses support for CCP Gotion battery plant
66 watching -
 3:10:39
3:10:39
GoodLawgic
12 hours agoThe Following Program: GREAT Lawgic Joins To Discuss Domestic Terrorism in 2025
131K82 -
 1:05:48
1:05:48
Mikhaila Peterson
6 days agoDoctor On The Carnivore Diet and Fertility | Robert Kiltz EP 218
89.4K35 -
 2:46:06
2:46:06
DDayCobra
15 hours ago $21.17 earnedCobraCast 199
89.4K19 -
 2:07:27
2:07:27
TheSaltyCracker
15 hours agoTrump Tower Bombed w/ Cybertruck ReeEEeE Stream 01-01-25
200K449 -
 8:15:58
8:15:58
FreshandFit
21 hours agoElon Musk BETRAYAL & Mass Censorship On X
247K107