Premium Only Content
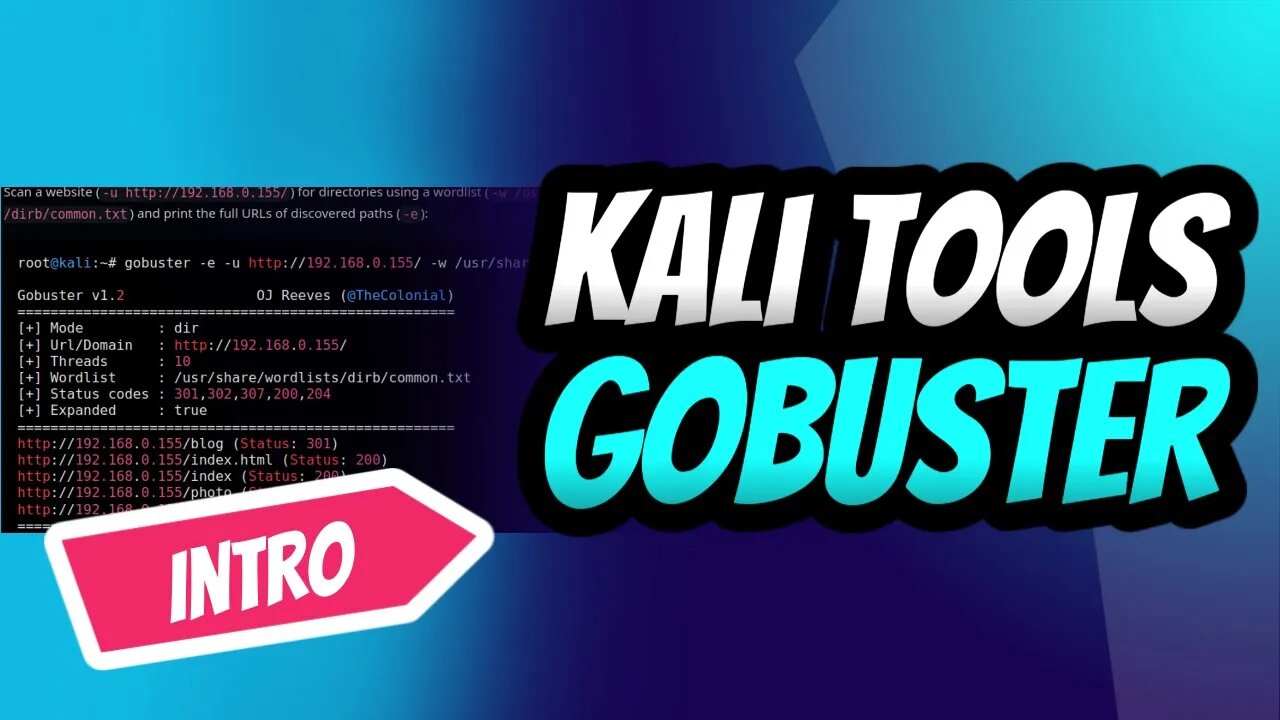
GoBuster for Ultimate Kali Linux Reconnaissance
Introduction into the power of GoBuster, the ultimate directory brute-forcing tool on Kali Linux! 🚀🔥 Learn how to reveal hidden directories and files, crack passwords, and uncover vulnerabilities with ease. Follow our step-by-step guide to mastering GoBuster and supercharge your ethical hacking skills.👩💻👨💻
Don't miss out on this essential intro for every aspiring hacker and penetration tester. Subscribe now, and let's get our hands dirty with GoBuster! 💪🔓
#KaliLinux #GoBuster #EthicalHacking #PenTesting #CyberSecurity #Reconnaissance #InfoSec #HiddenDirectories #BruteForce 💻🌐🔧🔒🕵️♀️🕵️♂️
Stay tuned for an upcoming detailed tutorial that will transform you into a GoBuster pro in no time! 🌟🔧
Subscribe and hit the bell icon to make sure you don't miss this comprehensive guide, and unlock your full potential as an ethical hacker and penetration tester. Let's explore the world of GoBuster together! 🌍🔓💡
If you look at the help command, we can see that Gobuster has a few modes.
dir — Directory enumeration mode.
dns — Subdomain enumeration mode.
fuzz — Fuzzing mode.
s3 — S3 enumeration mode.
v host — V host enumeration mode.
Gobuster is a fast brute-force tool to discover hidden URLs, files, and directories within websites. This will help us to remove/secure hidden files and sensitive data.
Gobuster also helps in securing sub-domains and virtual hosts from being exposed to the internet. Overall, Gobuster is a fantastic tool to help you reduce your application’s attack surface.
You can use the following steps to prevent and stop brute-force attacks on your web application.
Audit yourself: Use Gobuster on your own applications and perform an audit. This will help you find the information that will be visible to the attackers.
Apply security policies: To prevent resources like S3 from being exposed on the internet, use AWS bucket policies to prevent unauthorized access.
Use bot protection solutions: Bot protection services like Cloudflare will stop any brute-force attacks making it incredibly difficult to attack your web application.
-
 1:43
1:43
Dev Null - | Hacking| CyberSecurity| Cybersecurity education
1 year agoSelecting a Laptop for Ethical Hacking Success
1461 -
 6:48:50
6:48:50
Akademiks
14 hours agoKendrick Lamar and SZA disses Drake and BIG AK? HOLD UP! Diddy, Durk, JayZ update. Travis Hunter RUN
156K28 -
 11:45:14
11:45:14
Right Side Broadcasting Network
9 days agoLIVE REPLAY: TPUSA's America Fest Conference: Day Three - 12/21/24
340K28 -
 12:19
12:19
Tundra Tactical
14 hours ago $12.74 earnedDaniel Penny Beats Charges in NYC Subway Killing
62.8K12 -
 29:53
29:53
MYLUNCHBREAK CHANNEL PAGE
1 day agoUnder The Necropolis - Pt 1
153K52 -
 2:00:10
2:00:10
Bare Knuckle Fighting Championship
3 days agoCountdown to BKFC on DAZN HOLLYWOOD & FREE LIVE FIGHTS!
55.7K3 -
 2:53:01
2:53:01
Jewels Jones Live ®
1 day agoA MAGA-NIFICENT YEAR | A Political Rendezvous - Ep. 103
148K36 -
 29:54
29:54
Michael Franzese
18 hours agoCan Trump accomplish everything he promised? Piers Morgan Article Breakdown
134K57 -
 2:08:19
2:08:19
Tactical Advisor
22 hours agoThe Vault Room Podcast 006 | Farwell 2024 New Plans for 2025
198K11 -
 34:12
34:12
inspirePlay
1 day ago $6.00 earned🏆 The Grid Championship 2024 – Cass Meyer vs. Kelly Rudney | Epic Battle for Long Drive Glory!
95.7K8