Premium Only Content
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
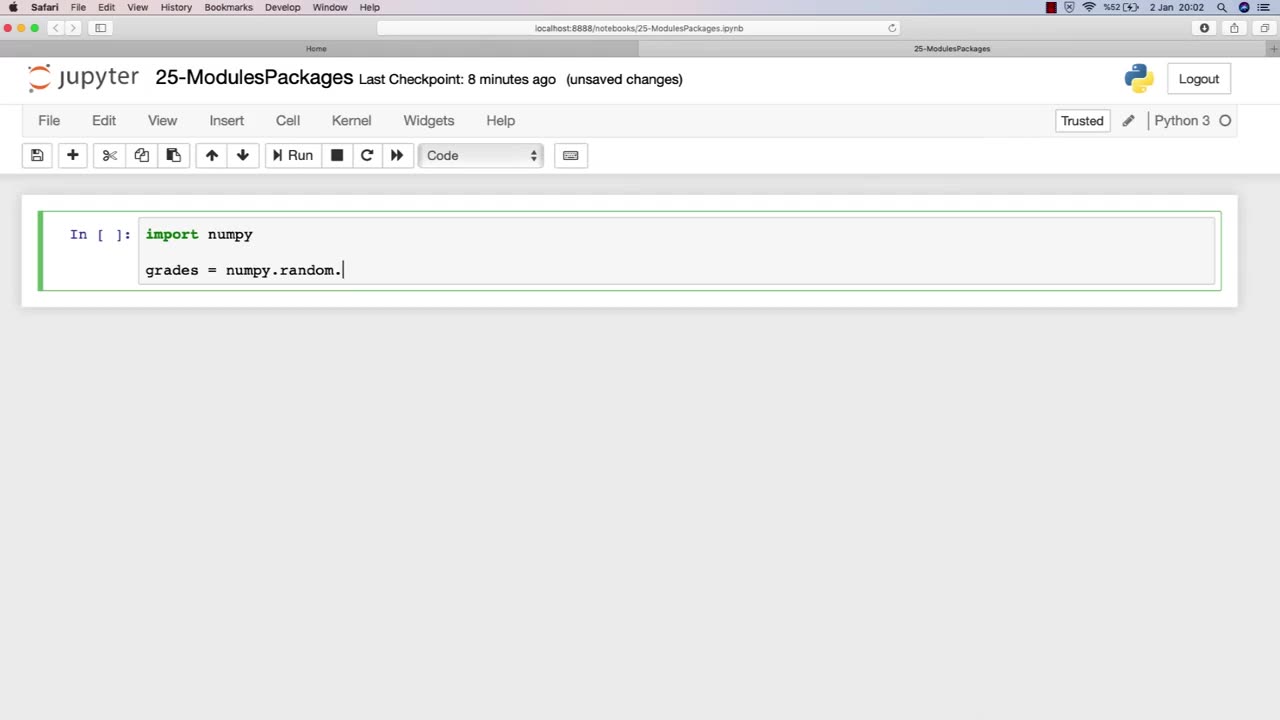
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 3:54:19
3:54:19
SpartakusLIVE
6 hours agoPUBG Duos w/ Viss || Tactical Strategy & HARDCORE Gameplay
47.9K1 -
 5:54:54
5:54:54
FRENCHY4185
7 hours agoFRENCHY'S BIRTHDAY BASH !!! THE BIG 40 !!!
64.1K3 -
 1:23:33
1:23:33
Michael Franzese
15 hours agoThings to look forward to in 2025
83.9K46 -
 3:23:02
3:23:02
I_Came_With_Fire_Podcast
16 hours agoDefeating VICTIMHOOD: Advocacy, Resiliency, and Overcoming Abuse
93.4K15 -
 2:00:56
2:00:56
Game On!
23 hours ago $10.20 earnedNFL Experts debate if Joe Burrow will make HISTORY in Week 18!
111K13 -
 2:07:57
2:07:57
InfiniteWaters(DivingDeep)
4 days agoHOW TO ENTER 2025 LIKE A BOSS!
41.5K1 -
 15:43
15:43
Tactical Advisor
9 hours agoBEST and WORST Guns Of 2024
31.7K8 -
 9:14
9:14
Dermatologist Dr. Dustin Portela
8 hours ago $1.07 earnedProducts a Dermatologist Actually Uses
28.6K10 -
 20:54
20:54
inspirePlay
10 hours ago $3.98 earned🏌️♀️ Extreme Knockout Golf Challenge Part 2 – Do the GIRLS beat the BOYS? 🏌️
50.1K2 -
 24:09
24:09
Squaring The Circle, A Randall Carlson Podcast
9 hours ago#033 At The Crossroads - Squaring the Circle: A Randall Carlson Podcast
33.2K12