Premium Only Content
Chapter-32, LEC-2 | Using Libraries | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
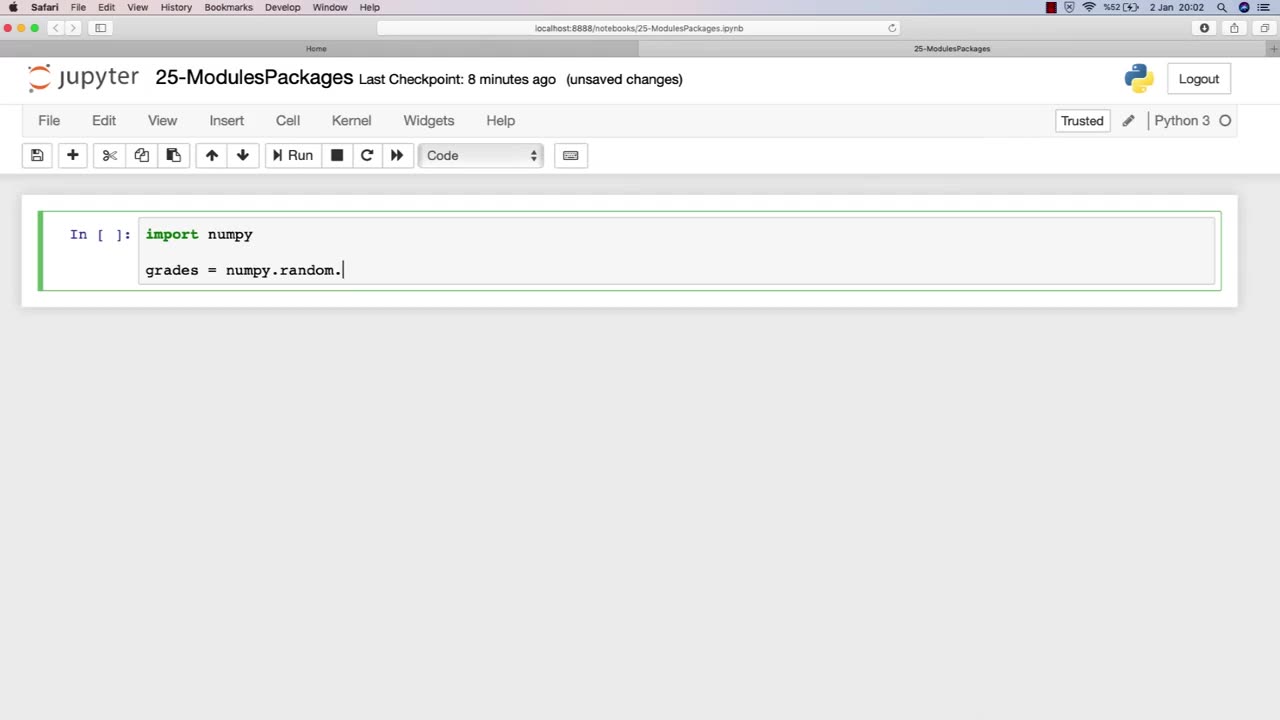
Libraries are an essential component of modules in ethical hacking, providing a collection of pre-written code that can be used to simplify and streamline the development of hacking tools and techniques. In the context of ethical hacking, libraries can provide a range of functionality, including network scanning, password cracking, and vulnerability exploitation.
The chapter on using libraries in an ethical hacking course book typically covers the basics of libraries, including how they work, their different types, and their importance in ethical hacking. This chapter may also provide an overview of various libraries commonly used in ethical hacking, such as Scapy for packet manipulation, Metasploit for vulnerability exploitation, and Nmap for network scanning.
Furthermore, this chapter may discuss the ethical considerations involved in using libraries for ethical hacking purposes, including the potential risks and legal implications of using pre-written code to conduct security testing. It may also emphasize the importance of understanding the limitations and potential pitfalls of using libraries, and the need for proper documentation and informed consent when using them in security testing.
Overall, the using libraries chapter in an ethical hacking course book is a valuable resource for ethical hackers, providing insight into how pre-written code can be leveraged to improve the efficiency and effectiveness of ethical hacking techniques. By understanding how libraries work and the ethical considerations involved in their use, ethical hackers can build more effective and responsible security testing processes.
-
 29:54
29:54
Michael Franzese
7 hours agoCan Trump accomplish everything he promised? Piers Morgan Article Breakdown
67.7K43 -
 2:08:19
2:08:19
Tactical Advisor
11 hours agoThe Vault Room Podcast 006 | Farwell 2024 New Plans for 2025
152K11 -
 34:12
34:12
inspirePlay
1 day ago $4.64 earned🏆 The Grid Championship 2024 – Cass Meyer vs. Kelly Rudney | Epic Battle for Long Drive Glory!
60.2K8 -
 17:50
17:50
BlackDiamondGunsandGear
9 hours ago $1.18 earnedTeach Me How to Build an AR-15
36.4K4 -
 9:11
9:11
Space Ice
1 day agoFatman - Greatest Santa Claus Fighting Hitmen Movie Of Mel Gibson's Career - Best Movie Ever
99.6K42 -
 42:38
42:38
Brewzle
1 day agoI Spent Too Much Money Bourbon Hunting In Kentucky
65.3K12 -
 1:15:30
1:15:30
World Nomac
17 hours agoMY FIRST DAY BACK in Manila Philippines 🇵🇭
49.5K9 -
 13:19
13:19
Dr David Jockers
1 day ago $9.81 earned5 Dangerous Food Ingredients That Drive Inflammation
70K17 -
 1:05:13
1:05:13
FamilyFriendlyGaming
1 day ago $15.59 earnedCat Quest III Episode 8
125K3 -
 10:39
10:39
Cooking with Gruel
2 days agoMastering a Succulent London Broil
80.9K5