Premium Only Content
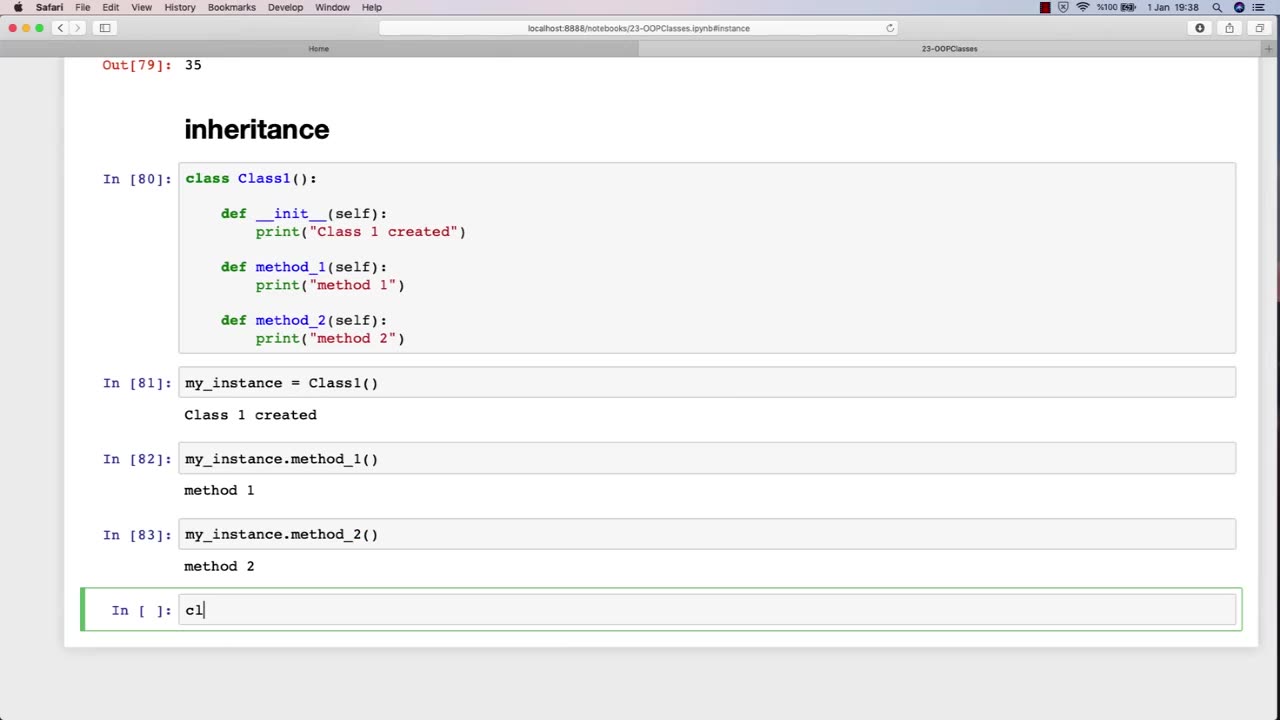
Chapter-31, LEC-5 | Inheritance | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking #funnelhackinglive #hackinglife #termuxhacking #learnhacking #bodyhacking #patternhacking #biohackingsuccess #ikeahacking #hackingorsecurity #russianhacking #traumahacking #shackingup #hackinghealth #growthhackingtips #wifihacking
Inheritance is an important concept in object-oriented programming, and it can also be relevant to an ethical hacking course. In the context of ethical hacking, inheritance can refer to the use of pre-existing code or tools to aid in the hacking process.
For example, ethical hackers may inherit code or tools from previous projects, open-source software, or online resources. This code or tools may help them automate tasks, test for vulnerabilities, or exploit known weaknesses. By inheriting code or tools, ethical hackers can save time and effort, while also benefiting from the knowledge and expertise of other developers.
However, it is important for ethical hackers to be aware of the potential risks and limitations of inheriting code or tools. Inherited code may contain bugs or vulnerabilities that could introduce new security risks, and inherited tools may not be well-suited to the specific context of the hacking project. Therefore, ethical hackers must exercise caution when using inherited code or tools, and should always verify their functionality and security before incorporating them into their own work.
Furthermore, ethical hackers must also consider the ethical implications of inheriting code or tools. They must ensure that the code or tools they use are legally obtained and do not infringe on intellectual property rights or other legal obligations. They must also be mindful of the potential impact of their actions, and ensure that they are using their skills and tools for ethical purposes.
In summary, inheritance is an important concept in ethical hacking, as it allows hackers to leverage pre-existing code or tools to aid in their work. However, ethical hackers must be aware of the potential risks and limitations of inherited code or tools, and must also consider the ethical implications of their actions.
-
 34:28
34:28
Tudor Dixon
3 hours agoHypocrisy and Accountability in Politics with Sen. Markwayne Mullin | The Tudor Dixon Podcast
1.08K1 -
 LIVE
LIVE
The Shannon Joy Show
3 hours ago🔥🔥Live EXCLUSIVE With Edward Dowd: Trump CANNOT Stop The Worldwide Economic Collapse🔥🔥
514 watching -
 1:03:32
1:03:32
The Dan Bongino Show
3 hours agoTrump Joins The Show To Drop Massive Truth Bombs (Ep. 2403) - 01/17/2025
483K878 -
 LIVE
LIVE
Right Side Broadcasting Network
3 days agoLIVE: RSBN Pre-Inauguration Coverage: Day Two Live from Washington D.C. - 1/17/25
2,755 watching -
 21:42
21:42
The Rubin Report
2 hours ago‘Piers Morgan’ Panelists' Jaws Drop as Liberal’s Entire Narrative Obliterated w/ One Question
44.4K25 -
 1:37:57
1:37:57
Steven Crowder
3 hours agoMAGA: T-Minus Three Days | Everything We Want President Trump to do on Day One
227K74 -
 1:14:04
1:14:04
Dave Portnoy
19 hours agoThe Unnamed Show With Dave Portnoy, Kirk Minihane, Ryan Whitney - Episode 42
48.5K5 -
 LIVE
LIVE
LFA TV
17 hours agoREBUILD PEDOWOOD! | LIVE FROM AMERICA 1.17.25 11am
5,098 watching -

Caleb Hammer
18 hours agoI've Never Hated A More Vile Piece of Trash | Financial Audit
20.7K -
 LIVE
LIVE
Benny Johnson
4 hours ago🚨 Trump Shuts DOWN The Border LIVE Right Now | Kristi Noem Confirmation Hearing For DHS, Deport!
13,403 watching