Premium Only Content
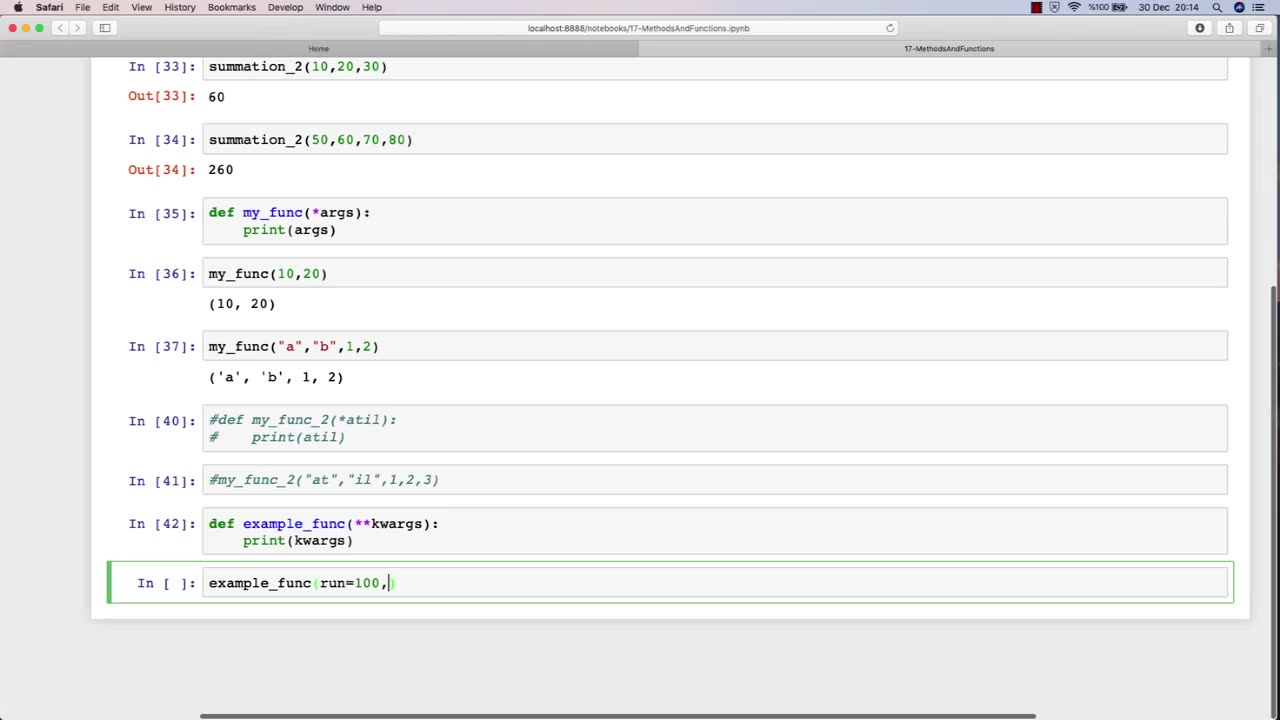
Chapter-30, LEC-4 | Functions Advanced | #rumble #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
The function of an advanced ethical hacking course is to provide experienced professionals with the latest knowledge, techniques, and tools in the field of cybersecurity. This course is designed for individuals who have already completed a basic ethical hacking course and are looking to enhance their skills and expertise in this rapidly evolving field.
The advanced ethical hacking course typically covers advanced topics such as exploit development, reverse engineering, cryptography, network forensics, and advanced penetration testing techniques. The course also provides students with in-depth knowledge of the latest cybersecurity threats and vulnerabilities, and how to defend against them.
One of the primary functions of an advanced ethical hacking course is to teach students how to develop and use custom exploits and tools to exploit vulnerabilities that may not be detected by commercial security tools. This requires a deep understanding of programming, scripting, and operating system internals.
In addition to technical skills, the advanced ethical hacking course also emphasizes the importance of soft skills, such as communication, documentation, and project management. Students learn how to effectively communicate their findings to technical and non-technical stakeholders, and how to manage complex ethical hacking projects from start to finish.
Overall, the function of an advanced ethical hacking course is to provide experienced professionals with the advanced knowledge and skills necessary to stay ahead of the curve in the constantly evolving field of cybersecurity. This course equips students with the tools and techniques needed to effectively identify and address the latest cybersecurity threats and vulnerabilities, and to help protect organizations from potentially devastating cyber attacks.
-
 7:56:34
7:56:34
Barry Cunningham
1 day agoWATCH LIVE: TRUMP INAUGURATION MAKE AMERICA GREAT AGAIN VICTORY RALLY - 1 DAY TO GO!!
86.9K55 -
 8:36
8:36
China Uncensored
15 hours agoIs China’s EV Industry Collapsing?
215K125 -
 4:17:00
4:17:00
Tundra Tactical
1 day ago $29.91 earnedSHOT SHOW 2025!!!!!! Whats Are We Looking Forward To Most
274K30 -
 22:53
22:53
Film Threat
1 day agoA TRIBUTE TO VISIONARY DIRECTOR DAVID LYNCH | Film Threat News
122K9 -
 20:30
20:30
Exploring With Nug
1 day ago $7.95 earnedMissing Father of 2 FOUND Underwater In Shallow Pond!
95.2K15 -
 19:19
19:19
This Bahamian Gyal
1 day agoThe View PRAISES Michelle Obama for DITCHING TRUMP inauguration, "when they go LOW, go even LOWER"
77.8K77 -
 14:25
14:25
Degenerate Jay
1 day ago $9.15 earnedThe Flash Movie Failed Because People Hate The Character? Sure.
162K26 -
 28:30
28:30
CharLee Simons Presents Do Not Talk
6 days agoSam Anthony from YourNews.com (with host CharLee Simons)
98.2K4 -
 52:34
52:34
PMG
1 day ago $5.94 earnedHannah Faulkner and Steve Friend | EXPOSE THE FBI CORRUPTION - KASH PATEL
72.2K9 -
 25:33
25:33
marcushouse
2 days ago $40.31 earnedStarship Exploded! What Went Wrong? Flight Test 7 Explained
225K103