Premium Only Content
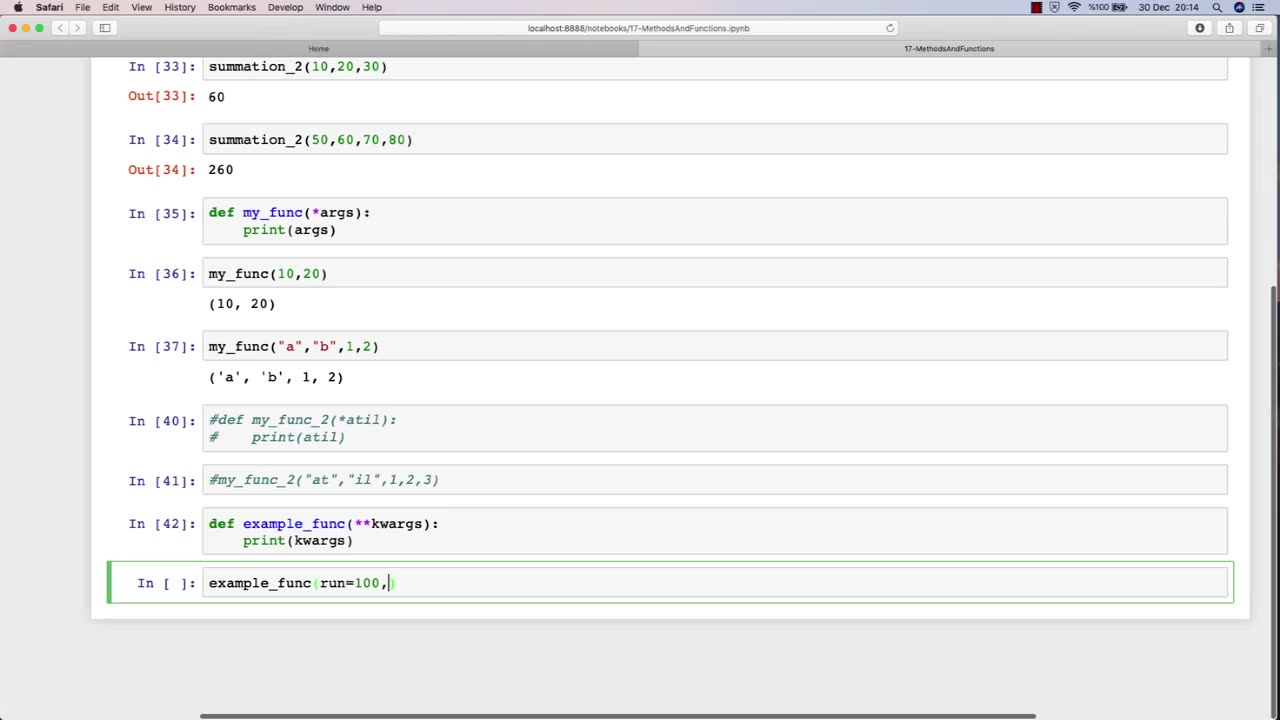
Chapter-30, LEC-4 | Functions Advanced | #rumble #ethicalhacking #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
The function of an advanced ethical hacking course is to provide experienced professionals with the latest knowledge, techniques, and tools in the field of cybersecurity. This course is designed for individuals who have already completed a basic ethical hacking course and are looking to enhance their skills and expertise in this rapidly evolving field.
The advanced ethical hacking course typically covers advanced topics such as exploit development, reverse engineering, cryptography, network forensics, and advanced penetration testing techniques. The course also provides students with in-depth knowledge of the latest cybersecurity threats and vulnerabilities, and how to defend against them.
One of the primary functions of an advanced ethical hacking course is to teach students how to develop and use custom exploits and tools to exploit vulnerabilities that may not be detected by commercial security tools. This requires a deep understanding of programming, scripting, and operating system internals.
In addition to technical skills, the advanced ethical hacking course also emphasizes the importance of soft skills, such as communication, documentation, and project management. Students learn how to effectively communicate their findings to technical and non-technical stakeholders, and how to manage complex ethical hacking projects from start to finish.
Overall, the function of an advanced ethical hacking course is to provide experienced professionals with the advanced knowledge and skills necessary to stay ahead of the curve in the constantly evolving field of cybersecurity. This course equips students with the tools and techniques needed to effectively identify and address the latest cybersecurity threats and vulnerabilities, and to help protect organizations from potentially devastating cyber attacks.
-
 12:53
12:53
BIG NEM
11 hours agoI Became a Virginity Expert. The Numbers Will SHOCK You.
1.74K -
 7:51
7:51
PerpetualHealthCo
19 hours agoW.H.O's In Charge?
1.91K1 -
 1:09:34
1:09:34
PMG
15 hours agoDoomsday Clock Moves Toward Midnight!!! Is The End Coming Sooner Than We Thought?!
2.21K2 -
 3:03:51
3:03:51
FreshandFit
9 hours agoShe BRAGGED About Her ABORTIONS?!
85.3K98 -
 1:45:26
1:45:26
Kim Iversen
14 hours agoBANNED for Telling the Truth: The 9/11 and Epstein Plot They Don't Want You To Hear
156K247 -
 1:08:47
1:08:47
Man in America
17 hours agoDr. Makis EXPOSES Big Pharma’s SICK Vaccine Scam—RFK Jr. Must Act NOW!
121K45 -
 1:28:21
1:28:21
Glenn Greenwald
15 hours agoRFK Jr. Hearing Reveals DC Pro-Pharma Consensus; Trump's Executive Order to Deport Student Protesters Criticizing Israel; Untangling DC Think Tank Funding & Influence | SYSTEM UPDATE #399
166K188 -
 1:23:44
1:23:44
Space Ice
15 hours agoSpace Ice & Redeye: Van Damme's The Quest: Pirates, Clowns, James Bond & Bloodsport
56.1K3 -
 59:57
59:57
The StoneZONE with Roger Stone
13 hours agoJ6 Martyr Enrique Tarrio Describes Inhumane Prison Conditions Ordered by Biden | The StoneZONE
54.8K4 -
 16:48
16:48
Tundra Tactical
12 hours ago $11.42 earnedAffordable Medical Gear From ACETAC SHOT Show 2025
111K5