Premium Only Content
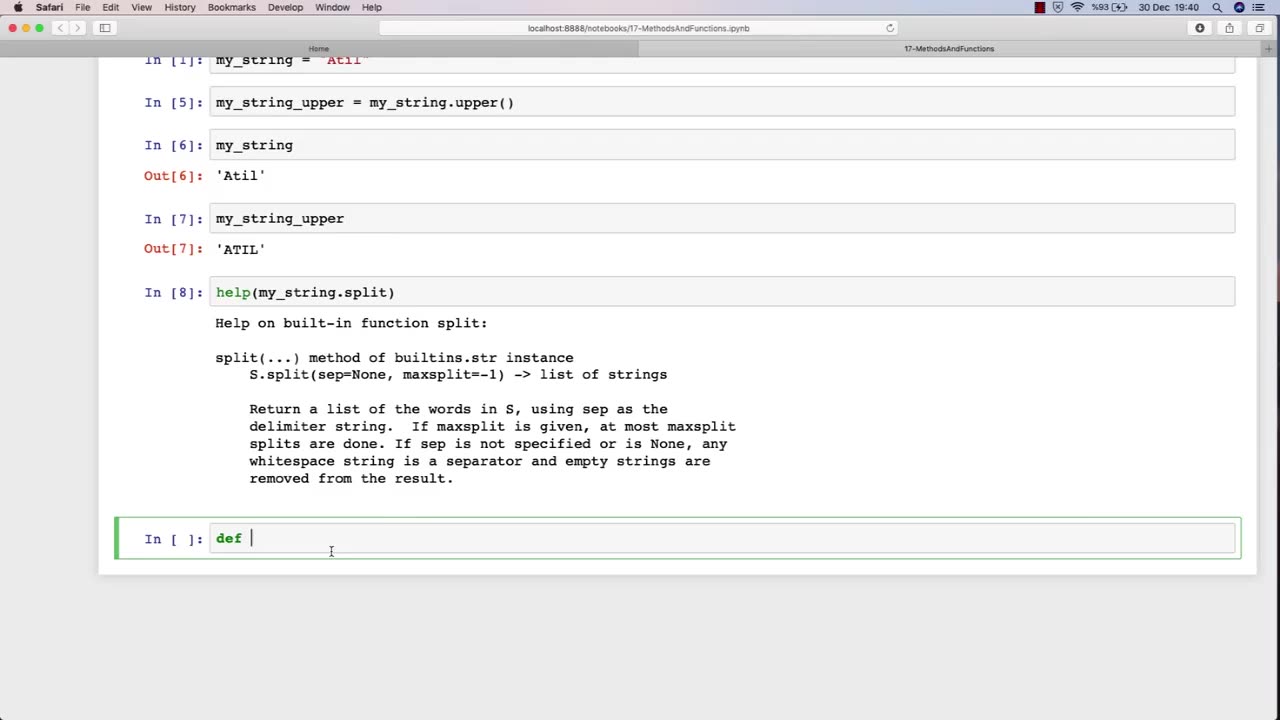
Chapter-30, LEC-2 | Functions Explained (lec-1) | #rumble #ethicalhacking #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy
The function of an ethical hacking course is to equip individuals with the knowledge, skills, and techniques necessary to become a professional ethical hacker. Ethical hacking is a critical component of cybersecurity, as it involves identifying and addressing potential vulnerabilities in computer systems, networks, and applications before malicious actors can exploit them.
An ethical hacking course typically covers a range of topics related to cybersecurity, including penetration testing, vulnerability assessment, network security, web application security, social engineering, cryptography, and incident response. The course provides students with an understanding of various security threats and how to mitigate them through the use of specialized tools and techniques.
During an ethical hacking course, students learn how to perform vulnerability assessments, conduct penetration testing, and analyze system and network logs to identify potential security threats. They also learn how to use various tools, such as vulnerability scanners and network analyzers, to assess the security posture of a system or network. Additionally, students learn about common attack vectors and techniques, such as SQL injection and cross-site scripting, and how to defend against them.
Overall, the goal of an ethical hacking course is to train individuals to become skilled and responsible cybersecurity professionals who can help organizations protect themselves from cyber attacks. By learning how to identify vulnerabilities and mitigate security threats, students can help ensure the security and privacy of sensitive information and safeguard against potential data breaches.
-
 LIVE
LIVE
The Charlie Kirk Show
44 minutes agoGaza Thoughts + DOGE The Destroyer | Sen. Schmitt, Benz | 2.5.2025
8,902 watching -
 LIVE
LIVE
Simply Bitcoin
1 hour agoNEW REPORT: Bitcoin ETF Insider Doubles Down on UNTHINKABLE 2030 prediction! | EP 1176
247 watching -
 59:36
59:36
The Dan Bongino Show
3 hours agoTrump Shocks The World With Major Announcement (Ep. 2416) - 02/05/2025
505K667 -
 1:19:04
1:19:04
The Rubin Report
2 hours agoTrump & Netanyahu Shock with Truly Unexpected Plan for Gaza
44.5K29 -
 1:59:23
1:59:23
Steven Crowder
3 hours ago🔴 Trump's Hitlist Grows: USAID, Dept. of Education, CIA, and... Gaza?
316K271 -
 LIVE
LIVE
Grant Stinchfield
56 minutes agoThe FBI Withholds 5000 Names of Agents & Employees Who Hunted Down J6'ers
272 watching -
 LIVE
LIVE
LFA TV
16 hours agoMA-GAZA STRIP! | LIVE FROM AMERICA 2.5.25 11am
6,435 watching -
 2:14:55
2:14:55
Matt Kohrs
10 hours agoBreaking Market News, Earnings Review & Live Trading $1M || The MK Show
66.9K1 -
 1:27:18
1:27:18
Caleb Hammer
2 hours agoRadical Femcel Is Literal Garbage | Financial Audit
16.5K1 -
 38:57
38:57
Rethinking the Dollar
1 hour agoEvery Signature Counts: How Trump's Policies Threaten the Dollar's Stability
32.1K5