Premium Only Content
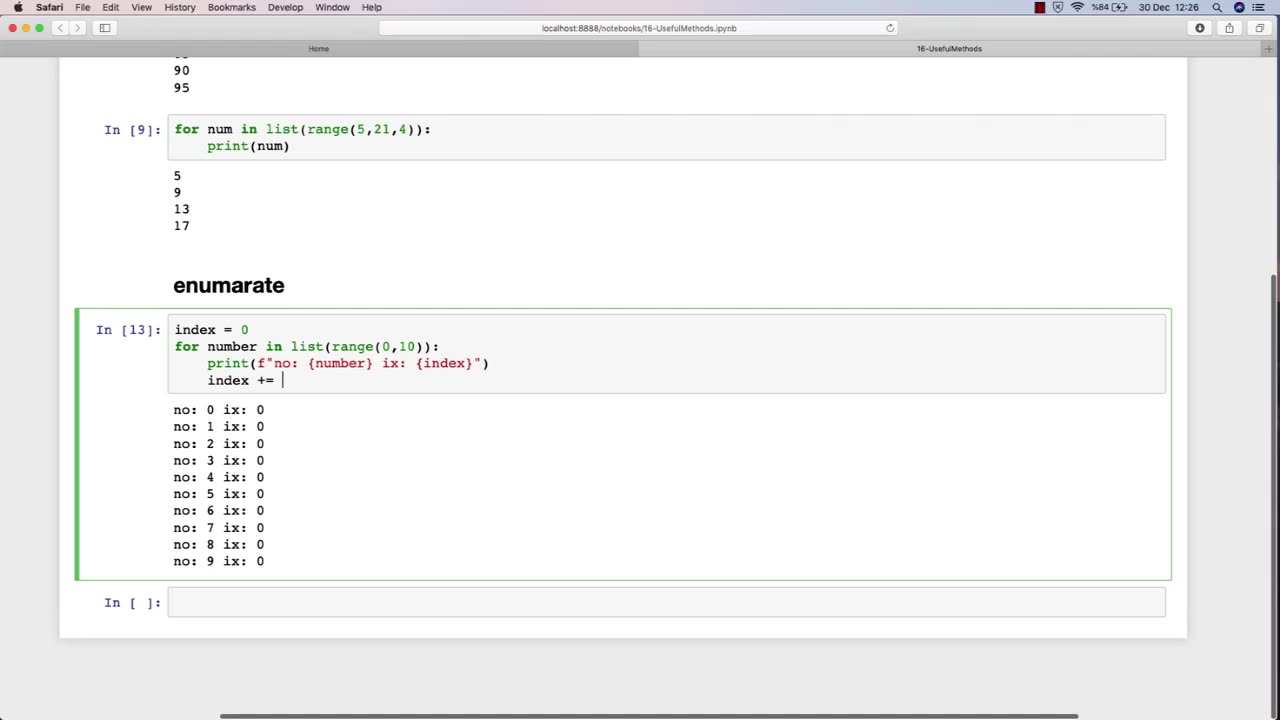
Chapter-29, LEC-2 | Useful Methods #hacking #growthhacking #ethicalhacking #rumble #education
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools
#bushwhacking #hacking_or_secutiy #porthacking#porthacking #belajarhacking
It is a crucial part of cybersecurity and helps organizations in protecting their sensitive information from malicious attackers.
One of the most essential topics in an ethical hacking course is the use of various methods and tools for conducting effective security assessments. One such useful method is the use of penetration testing.
Penetration testing is a simulated attack on a computer system or network to identify vulnerabilities that a malicious attacker could exploit. This method involves using various hacking techniques and tools to try to gain access to the system or network. Penetration testing is a comprehensive approach to testing a system's security and can help identify potential weaknesses that can be addressed before they can be exploited by malicious attackers.
Another important topic in an ethical hacking course is the use of vulnerability scanners. Vulnerability scanners are automated tools that scan a computer system or network to identify vulnerabilities that can be exploited by attackers. These tools can help identify issues such as outdated software, weak passwords, and misconfigured settings.
Social engineering is another useful method that ethical hackers use to identify vulnerabilities in a system or network. Social engineering involves manipulating individuals into divulging sensitive information or performing actions that can compromise the security of a system. This technique can help identify weaknesses in an organization's security policies and training programs.
Overall, ethical hacking courses teach various methods and techniques that can be used to identify vulnerabilities in computer systems and networks. By using these methods, ethical hackers can help organizations strengthen their security measures and protect their sensitive information from malicious attackers.
-
 LIVE
LIVE
The Charlie Kirk Show
8 minutes agoThe Bravest Presidential Action In Decades + Trump's Spiritual Rebirth | Sen. Mullin | 1.22.2025
3,884 watching -

The Dan Bongino Show
3 hours agoPresident Trump Did More In A Day Than Others Did In Two Terms (Ep. 2406) - 01/22/2025
231K329 -
 57:21
57:21
Russell Brand
2 hours agoBREAK BREAD EP. 11 - NATHAN FINOCHIO
42K2 -
 LIVE
LIVE
Steven Crowder
3 hours ago🔴 Non-Stop Winning: How Trump Axed DEI & the Unholy Sermon at the National Cathedral
39,174 watching -
 59:11
59:11
The Rubin Report
1 hour agoWatch the Moment Charlamagne tha God Realizes Dems Have Been Lying the Whole Time
10.1K10 -
 LIVE
LIVE
Right Side Broadcasting Network
22 hours agoLIVE: RSBN Post-Inauguration Coverage - 1/22/25
5,073 watching -
 LIVE
LIVE
LFA TV
16 hours ago$3 TRILLION IN 3 DAYS! | LIVE FROM AMERICA 1.22.25 11am
6,088 watching -
 UPCOMING
UPCOMING
Grant Stinchfield
17 minutes agoD.C. Judge Defies Trump! J6ers Still Being Held Hostage Despite Pardon!
-
 UPCOMING
UPCOMING
The Shannon Joy Show
1 hour ago🔥🔥WARP SPEED 2.0 On Steroids! Trump Announces STARGATE ‘The LARGEST AI Infrastructure Project In History’ To Expand mRNA Tech & Surveillance🔥🔥
2751 -
 LIVE
LIVE
Tudor Dixon
1 hour agoDementia: A Growing Concern for America | The Tudor Dixon Podcast
67 watching