Premium Only Content
Chapter-27, LEC-3 | Variables | #rumble #ethicalhacking #education #hacking
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram #growthacking #biohackingsecrets #realityhacking #neurohacking #hackingnews #funnelhacking #mindhacking
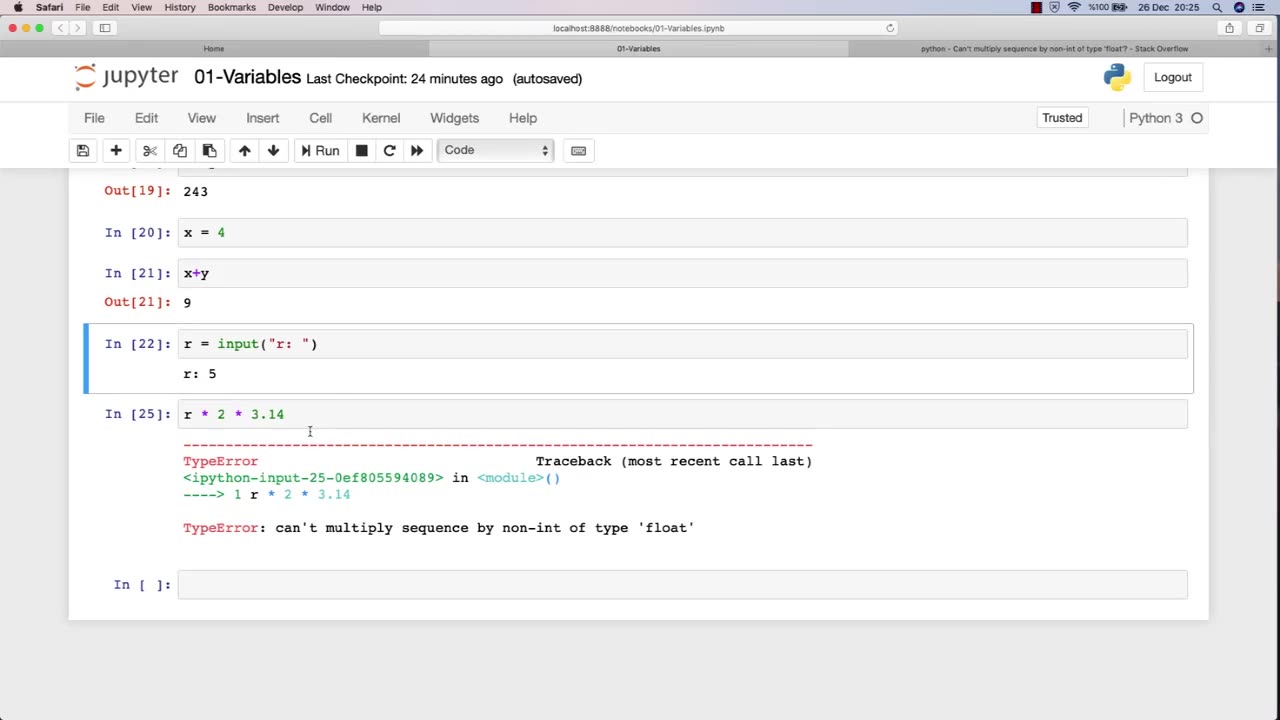
Variables are fundamental to programming, and they play a crucial role in ethical hacking. A variable is a storage location that holds a value or a reference to a value, and it can be manipulated by a program or script. In ethical hacking, variables are used to store and manipulate various types of data that are essential for carrying out attacks, testing security, and analyzing vulnerabilities.
Here are some examples of how variables are used in ethical hacking:
Target variables: These variables store information about the target system or network, such as IP addresses, domain names, and operating system versions. Ethical hackers use these variables to identify vulnerabilities and potential attack vectors.
Payload variables: These variables store the data or commands used in an attack, such as code snippets, exploit payloads, or malicious scripts. Ethical hackers use these variables to execute attacks, test security controls, and assess the effectiveness of countermeasures.
Password variables: Password variables store the passwords used to access computer systems and networks. Ethical hackers use password variables to test the strength of passwords, identify weak passwords, and crack passwords using various techniques.
Encryption variables: These variables store encryption keys, algorithms, and other information related to encryption. Ethical hackers use these variables to test the strength of encryption, identify vulnerabilities, and analyze weaknesses in encryption systems.
Environment variables: These variables store information about the system or network environment, such as system paths, environment variables, and configuration settings. Ethical hackers use these variables to analyze system configurations, identify vulnerabilities, and assess the security posture of a system or network.
Overall, variables are an essential component of ethical hacking, and a strong understanding of how to work with variables is crucial for success in this field. By effectively using variables, ethical hackers can more efficiently and effectively identify and address vulnerabilities in computer systems and networks.
-
 56:02
56:02
Sarah Westall
11 hours agoBiohacking & Peptides: Weight loss, Anti-Aging & Performance – Myth vs Reality w/ Dr. Diane Kazer
48.9K14 -
 11:22
11:22
Bearing
21 hours ago"Anxious & Confused" Federal Workers FREAK OUT Over DOGE Efficiency Email 💥
72.9K74 -
 1:31:20
1:31:20
Flyover Conservatives
1 day agoUS STOCK MARKET: Sinking Ship - Dr. Kirk Elliott; How I Fought Back Against Woke Schools & Stopped Gender Bathrooms - Stacy Washington | FOC Show
72.8K4 -
 1:08:09
1:08:09
Donald Trump Jr.
15 hours agoFBI Dream Team, Plus Taking Your Questions Live! | Triggered Ep.219
213K284 -
 7:32:37
7:32:37
Akademiks
15 hours agoDrake and PartyNextDoor '$$$4U' Album Sells 250K first week. BIG AK IS BACK.
128K18 -
 3:12:08
3:12:08
MyronGainesX
14 hours ago $32.98 earnedDan Bongino Named FBI Deputy Director, Trump Meets Macron, And More!
103K32 -
 3:12:31
3:12:31
vivafrei
13 hours agoBarnes Live from Seattle - Defending Benshoof in a Case that is CRAY CRAY!
177K54 -
 2:12:12
2:12:12
Robert Gouveia
14 hours agoLiberals EXPLODE over Elon's Email; Lawsuits FLY; Sanctions?? Congrats Dan!
127K78 -
 1:33:36
1:33:36
Redacted News
14 hours agoBREAKING! PUTIN LAUNCHES MASSIVE OFFENSIVE IN UKRAINE AS EUROPEAN LEADERS PUSH FOR MORE WAR
202K280 -
 44:39
44:39
Kimberly Guilfoyle
15 hours agoBetter Days Ahead for the FBI, Live with Asm Bill Essayli & John Koufos | Ep.199
127K34