Premium Only Content
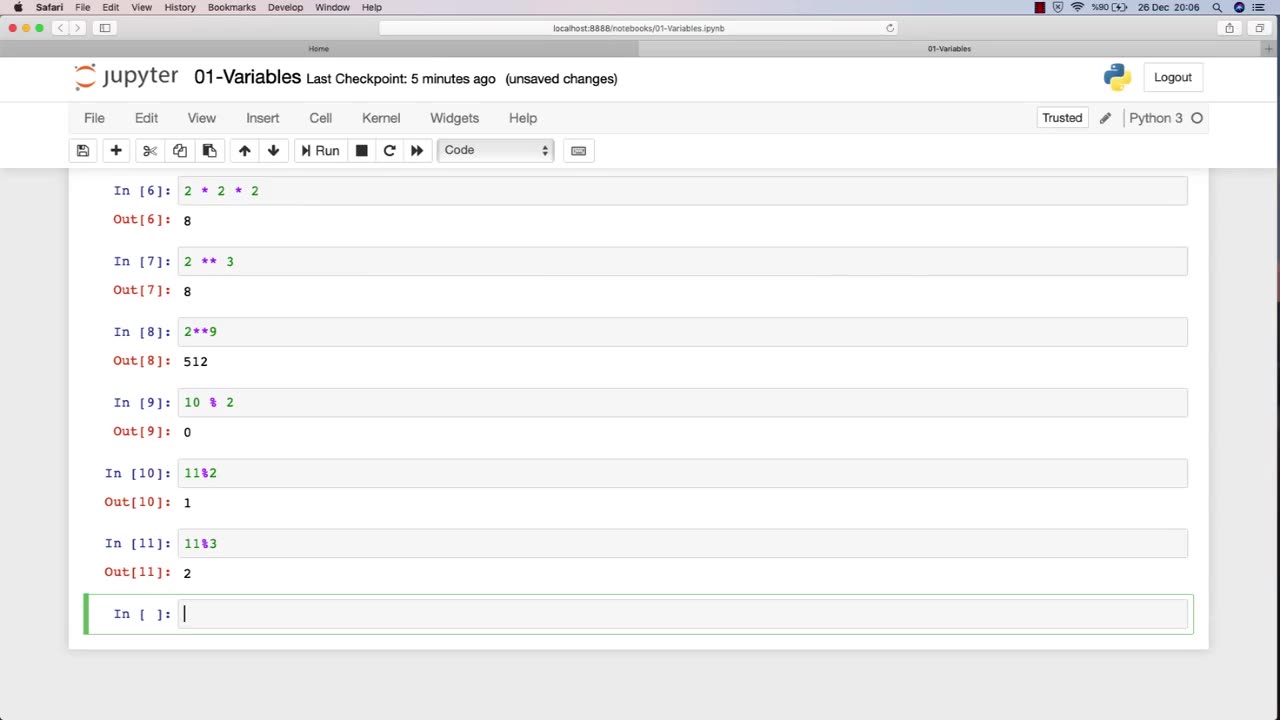
Chapter-27, LEC-2 | Numbers | #ethicalhacking #hacking #education #cybersport #cybersecurity
#ethicalhacking #hacking #rumble #virel #trending #education
Subscribe to our channel YouTube channel.❤️
/@thecybersecurityclassroom
Followe me on Rumble.💕
/@the1cybersequrityclassroom
#hacking #growthhacking #biohacking #ethicalhacking #lifehacking #whacking #hackingout #happyhacking #brainhacking #travelhacking #househacking #brainhackingum #hackingtools #bushwhacking #hacking_or_secutiy #porthacking #belajarhacking #hackinginstagram
Ethical hacking is a field that involves the use of various techniques and tools to identify and address vulnerabilities in computer systems and networks. Numbers play a critical role in ethical hacking, and understanding how to work with numbers is essential for success in this field.
Here are some examples of how numbers are used in ethical hacking:
IP Addresses: IP addresses are used to identify network devices and are essential for ethical hackers to understand. Ethical hackers use IP addresses to scan for open ports, identify potential vulnerabilities, and carry out attacks.
Ports: Ports are used to establish connections between devices on a network. Ethical hackers use knowledge of port numbers to scan for vulnerabilities, carry out attacks, and test the security of a network.
Passwords: Passwords are often used to protect sensitive information in computer systems and networks. Ethical hackers use various techniques to crack passwords, such as brute-force attacks, dictionary attacks, and rainbow table attacks.
Encryption: Encryption is the process of converting data into a secure format that cannot be read by unauthorized parties. Ethical hackers use their understanding of encryption algorithms and techniques to identify vulnerabilities and weaknesses in encryption systems.
Binary and hexadecimal: Binary and hexadecimal are number systems used in computing. Ethical hackers use their understanding of these number systems to analyze and manipulate data at the low-level, such as reverse engineering software or discovering vulnerabilities in firmware.
Overall, a strong understanding of numbers is essential for success in ethical hacking. By understanding how numbers are used in this field, ethical hackers can more effectively identify and address vulnerabilities in computer systems and networks.
-
 9:10
9:10
ariellescarcella
12 hours agoI Asked People To Toss Out An Identity : The Queer Alphabet Is OVER
5.48K5 -
 27:00
27:00
Squaring The Circle, A Randall Carlson Podcast
19 hours agoSPECIAL EPISODE: #037 Randall Carlson Explains The Vital Role of Sacred Geometry in the Modern Age
6.26K2 -
 58:35
58:35
Trumpet Daily
21 hours ago $3.93 earnedThe Trade War Begins - Trumpet Daily | Feb. 3, 2025
20.6K34 -
 47:03
47:03
Uncommon Sense In Current Times
18 hours agoArrested For Praying Silently in Western Culture and Convicted
13K1 -
 44:19
44:19
PMG
16 hours ago $0.01 earnedIn the wake of a tragedy! Finding hope in broken times
8.34K -
 3:40:50
3:40:50
FreshandFit
10 hours agoGirls Walk Off Pod After Being Exposed As Thots By Chat! 🤣
111K120 -
 5:30:06
5:30:06
SpartakusLIVE
14 hours ago#1 King of Content kicks off YOUR week with Monday MOTIVATION
133K8 -
 5:56:52
5:56:52
Akademiks
12 hours agoKendrick Lamar Sweeps Grammys. Drake announces new album on Feb 14. Rocky Trial Might get Dismissed?
106K6 -
 3:25:02
3:25:02
BrancoFXDC
10 hours ago $3.40 earnedWarzone Rebirth Rounds
48.9K -
 1:44:14
1:44:14
Glenn Greenwald
17 hours agoRubio's Shift: What is Trump's Foreign Policy? Trump/Musk Attack CIA Fronts USAID & NED: With Mike Benz | SYSTEM UPDATE #401
113K114